Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to combine two events based on common field?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi everyone,
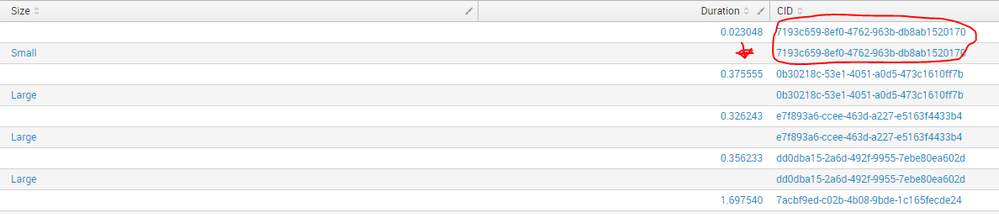
I am using splunk for about two week at my work and I have task to build dashboard. I have splunk query that extracts data from 2 different events but in the same source. The events share common ID. I am trying to combine the events based on the ID and represent the data from both events in a dashboard. I tried with multisearch and by. None of them worked. Can anyone give me a hit on how to approach this problem? Here is the query and a screen shot from the result:
index=?????? sourcetype=???? host=????? source=????????? "Number of Clients" OR "Duration:: in "
| rex field=_raw "Number of Clients: (?<ClientCount>\d+)"
| rex field=_raw "cid:(?<CID>\w+-\w+-\w+-\w+-\w+)"
| rex field=_raw "Duration:: in (?<Duration>\d+.\d+)"
| eval Size = if(ClientCount == 0, "Not part of association", if(ClientCount <= 3, "Small", if(ClientCount <= 10 ,"Medium",if (ClientCount > 10, "Large", ClientCount))))
| table Size Duration CID
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Got it working. Here is the solution
index=??? sourcetype=??? host=???? source=???? ("Number of Clients" OR "Duration:: in ")
| rex field=_raw "Number of Clients: (?<ClientCount>\d+)"
| rex field=_raw "cid:(?<CID>\w+-\w+-\w+-\w+-\w+)"
| rex field=_raw "Duration:: in (?<Duration>\d+.\d+)"
| eval Size = if(ClientCount == 0, "Not part of association", if(ClientCount <= 3, "Small", if(ClientCount <= 10 ,"Medium",if (ClientCount > 10, "Large", ClientCount))))
| stats values(Duration) as Duration values(Size) as Size by CID
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Got it working. Here is the solution
index=??? sourcetype=??? host=???? source=???? ("Number of Clients" OR "Duration:: in ")
| rex field=_raw "Number of Clients: (?<ClientCount>\d+)"
| rex field=_raw "cid:(?<CID>\w+-\w+-\w+-\w+-\w+)"
| rex field=_raw "Duration:: in (?<Duration>\d+.\d+)"
| eval Size = if(ClientCount == 0, "Not part of association", if(ClientCount <= 3, "Small", if(ClientCount <= 10 ,"Medium",if (ClientCount > 10, "Large", ClientCount))))
| stats values(Duration) as Duration values(Size) as Size by CID
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
very good,
if it works for you, kindly mark the answer as accepted, and upvote ant helpful comments if any so others will know this solution worked for you.
thanks and happy splunking!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
try this:
index=?????? sourcetype=???? host=????? source=????????? "Number of Clients" OR "Duration:: in "
| rex field=_raw "Number of Clients: (?\d+)"
| rex field=_raw "cid:(?\w+-\w+-\w+-\w+-\w+)"
| rex field=_raw "Duration:: in (?\d+.\d+)"
| eval Size = if(ClientCount == 0, "Not part of association", if(ClientCount <= 3, "Small", if(ClientCount <= 10 ,"Medium",if (ClientCount > 10, "Large", ClientCount))))
| stats values(CID) as CID by Duration SIze
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Doesn't return any result. Thanks for the reply.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
try Size i hade it with CAPITAL I there by accident