- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How to change a search query in the Splunk Ins...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
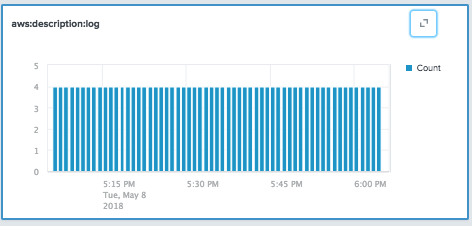
Currently I have incoming events (from logs). The predefined charts look like histogram of count of events for a specific period. How can I change conditions of search query?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can change the time-picker in the upper-left corner to change the time range. You can change some parameters of the histogram with the side panel on the right. Outside of that, SII doesn't have further graph customization at this time.
To expand events and explore the log data, click on the button in the upper-right corner.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can change the time-picker in the upper-left corner to change the time range. You can change some parameters of the histogram with the side panel on the right. Outside of that, SII doesn't have further graph customization at this time.
To expand events and explore the log data, click on the button in the upper-right corner.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok
Thanks
I'll be waiting for the further customizations in the new versions of SII. It would be a usefull feature to create own charts
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What kind of charts are you looking to create? Do you want general access to the SPL query language for customization or would you like this to be a part of the UI?