Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How do you add percentage of total for several col...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi all,
I'm quite new to Splunk and I'm struggling trying to add percentages to a table that I built from two indexes (sorry if the same question has been already asked, but I didn't find any applicable to my case).
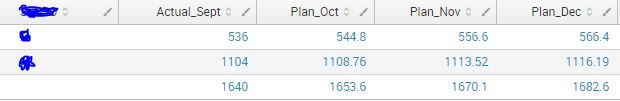
The table I have looks like this:
What I'm trying to do now is add, for each column, percentages of total: for example Actual_Sept % = 536 /1640 and 1104 / 1640 and so on for all columns
Hope you can help on this,
thanks anyway
Alessandro
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@alessandrocicchella,
If you could remove addcoltotals from your search, give this a try
"Your search without addcoltotals (or the last row) " |eventstats sum(*) as sum_*
|foreach * [eval <<FIELD>>_%=<<FIELD>>/sum_<<FIELD>>]|fields - sum_*
If this does not work, please provide the search used to find the current count/values under each field, we shall try alternative/better searches.
What goes around comes around. If it helps, hit it with Karma 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
With the eval command is quite simple to do that; something like:
| eval Percentage= round(100 * Count / Total,2)
However I don't understand how you are using the fields in your table; if i understood correctly the "Actual_Sept" field has in it the values of both the dividend and the divisor. Is that correct?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@alessandrocicchella,
If you could remove addcoltotals from your search, give this a try
"Your search without addcoltotals (or the last row) " |eventstats sum(*) as sum_*
|foreach * [eval <<FIELD>>_%=<<FIELD>>/sum_<<FIELD>>]|fields - sum_*
If this does not work, please provide the search used to find the current count/values under each field, we shall try alternative/better searches.
What goes around comes around. If it helps, hit it with Karma 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Renjith,
it works great 😄
Thank you very much for your fast and effective help