Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How do I plot a static value over time that is...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
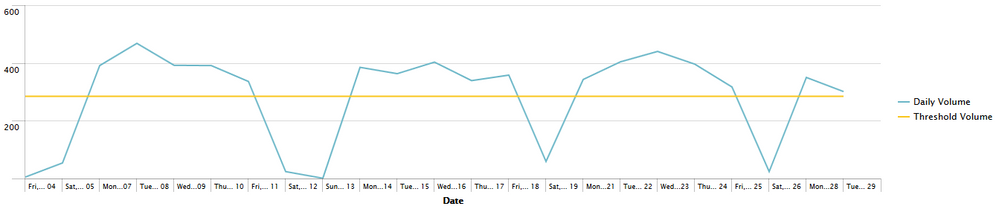
I'd like to plot in a timechart the count of events over the last 30 days.
In addition to this, I'd like another line which plots a line over the same period from a static value which is derived from the total of counts over the last month / 22.
Whilst I have no problem displaying the count of events over 30 days, I'm unsure as to how to plot a static value (ie. calculate a static value and plot it against all times as a threshold).
The following displays the average based on monthly count.
[[search>]] earliest=-30d@d latest=@d
| bucket _time span=1d | stats count as Volume by _time | rename _time As Date | eval Date = strftime(Date, "%a, %b %d")
| eventstats avg(Volume) as "Threshold Volume" | rename Volume as "Daily Volume"
However I actually want the 'Threshold Volume' to instead be derived from Volume / 22.
Thanks in advance for your help
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this
[[search>]] earliest=-30d@d latest=@d
| bucket _time span=1d | stats count as Volume by _time | rename _time As Date | eval Date = strftime(Date, "%a, %b %d")
| eventstats sum(Volume) as "Threshold Volume" | eval "Threshold Volume"='Threshold Volume' / 22| rename Volume as "Daily Volume"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this
[[search>]] earliest=-30d@d latest=@d
| bucket _time span=1d | stats count as Volume by _time | rename _time As Date | eval Date = strftime(Date, "%a, %b %d")
| eventstats sum(Volume) as "Threshold Volume" | eval "Threshold Volume"='Threshold Volume' / 22| rename Volume as "Daily Volume"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. That did the trick.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
just add this to the end of your current search:
... | eval "new Threshhold" = 'Threshold Volume' / 22
This simply calculates the value you want and puts it in a new field.
If you want the total Volume / 22 instead of the avg Volume / 22 as Threshold you need to change the avg in your eventstats to sum.
Greetings
Tom
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks Tom. Replacing avg() with sum() worked.