Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How can I create a visual depiction of when a devi...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have two separate events that logs a turn on and a turn off. I want to create a timechart showing when the device is on and off over a period of time. I only get a single event each time the state changes. How can I continue the state over time until a new state is recorded?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@landster, you would need to provide you sample event and your current search for us to assist you better.
However, based on the description provided, if you have state field with value ON and OFF at certain time intervals, you can try the filldown command to use the value of state from the previous event in the same time series.
<yourCurrentQuery>
| filldown state
| eval state_value=if(state=="ON",1,0)
| timechart span=1h sum(state_value) as value
Following is a run anywhere example with state as OFF at 0th hour (1st event) and ON at 9th Hour and finally OFF again at 19th Hour. PS: Commands from | gentimes till | eval state generate dummy data (run for Yesterday in the time picker):
| gentimes start=-1 end=0 increment=1h
| fields starttime
| eval _time=starttime
| fields _time
| eval date_hour=strftime(_time,"%H")
| eval state=case(date_hour=="00","OFF",date_hour=="09","ON",date_hour=="19","OFF")
| filldown state
| eval state_value=if(state=="ON",1,0)
| timechart span=1h sum(state_value) as value
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
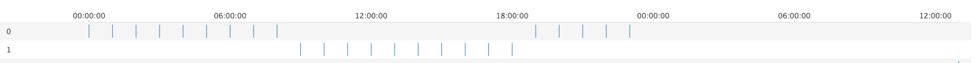
Using the search provided by @niketnilay, you could use a timeline visualization to represent this.
https://splunkbase.splunk.com/app/3120/
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is it possible to use the internal logs instead?? That way you can check for a phonehome event within your polling interval. If the event exists then the device is on, if not the device is off.
index=_* host=yourHostFilter phonehome
| timechart span=30m count by host
| foreach *
[eval <<FIELD>>IsOn = if(<<FIELD>> > 0, 1, 0)
| eval <<FIELD>>IsOff = if(<<FIELD>> = 0, 1, 0)
]
| fields + *IsOn + *IsOff
As long as you have a span that is >= your phone home interval this should work. Thanks.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@landster, you would need to provide you sample event and your current search for us to assist you better.
However, based on the description provided, if you have state field with value ON and OFF at certain time intervals, you can try the filldown command to use the value of state from the previous event in the same time series.
<yourCurrentQuery>
| filldown state
| eval state_value=if(state=="ON",1,0)
| timechart span=1h sum(state_value) as value
Following is a run anywhere example with state as OFF at 0th hour (1st event) and ON at 9th Hour and finally OFF again at 19th Hour. PS: Commands from | gentimes till | eval state generate dummy data (run for Yesterday in the time picker):
| gentimes start=-1 end=0 increment=1h
| fields starttime
| eval _time=starttime
| fields _time
| eval date_hour=strftime(_time,"%H")
| eval state=case(date_hour=="00","OFF",date_hour=="09","ON",date_hour=="19","OFF")
| filldown state
| eval state_value=if(state=="ON",1,0)
| timechart span=1h sum(state_value) as value
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Base Search:
index=ftgv2 sourcetype=FTGTVon* OR sourcetype=FTGTVoff*
| transaction terminalAddress startswith=(eventName=FTGTVOff) endswith=(eventName=FTGTVOn)
I am getting 2 events, one for TVOn and one for TVOff. They record the specific event and time by an identification number (terminalAddress). x axis would be time and y would be 1 for ON and 0 for OFF.
Does that make sense?