Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Getting count of field instead of a list of them
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Getting count of field instead of a list of them
rkaakaty
Path Finder
06-22-2017
07:32 AM
Hello,
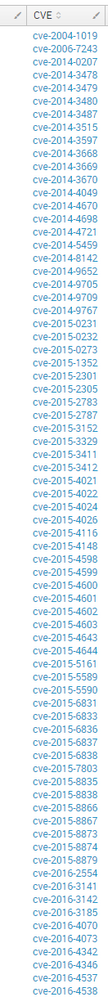
I am getting a stack of CVE field values, I just wanted to display the number of them (count). Here is my code:
index=nessus cve=*
| eval CVSS_SCORE = cvss_base_score + cvss_temporal_score
| eval description=substr(description,1,100)
| eval solution=substr(solution,1,100)
| rename id as ID, cve as CVE, plugin_name as Plugin_Name, description as Description, solution as Solution
| table ID, Plugin_Name, Description, CVE, Solution, CVSS_SCORE
| sort - CVSS_SCORE
This is what it looks like
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
DalJeanis
Legend
06-22-2017
07:56 AM
| stats count as CVECount
or
| stats dc(CVE) as CVECount
You don't really need much of that if all you want is the count of CVEs...
index=nessus cve=*
| fields cve
| dedup cve
| stats dc(cve) as CVECount
And if cve is an indexed field, then tstats would probably be more efficient
tstats where index=nessus AND cve=*
| stats dc(cve) as CVECount
Get Updates on the Splunk Community!
Data Management Digest – December 2025
Welcome to the December edition of Data Management Digest!
As we continue our journey of data innovation, the ...
Index This | What is broken 80% of the time by February?
December 2025 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with this ...
Unlock Faster Time-to-Value on Edge and Ingest Processor with New SPL2 Pipeline ...
Hello Splunk Community,
We're thrilled to share an exciting update that will help you manage your data more ...