Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Getting Average for this search
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
tefa627
Explorer
08-24-2020
07:39 AM
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
08-24-2020
08:01 AM
Hi
could you try this
....
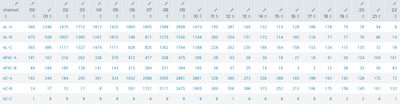
| chart eval(count(<your field name>)/7) AS field_div_by_7 by channel time_hourr. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
08-24-2020
08:01 AM
Hi
could you try this
....
| chart eval(count(<your field name>)/7) AS field_div_by_7 by channel time_hourr. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
tefa627
Explorer
09-11-2020
02:13 PM
How would I round the results?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
09-12-2020
12:56 AM
Time by time you must add ’ to surround <<FIELD>> to get SPL to known that it’s a field like
| foreach * [ eval <<FIELD>> = round(‘<<FIELD>>’,2)]
r. Ismo
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Announcing Modern Navigation: A New Era of Splunk User Experience
We are excited to introduce the Modern Navigation feature in the Splunk Platform, available to both cloud and ...
Modernize your Splunk Apps – Introducing Python 3.13 in Splunk
We are excited to announce that the upcoming releases of Splunk Enterprise 10.2.x and Splunk Cloud Platform ...
Step into “Hunt the Insider: An Splunk ES Premier Mystery” to catch a cybercriminal ...
After a whole week of being on call, you fell asleep on your keyboard, and you hit a sequence of buttons that ...