- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Do we have any Tarrask Malware detection queries f...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do we have any Tarrask Malware detection queries for Splunk Enterprise?
Do we have any Tarrask Malware detection queries for Splunk Enterprise?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Tomu521 - You can use Sysmon to monitor the registry and then create an alert based on that.
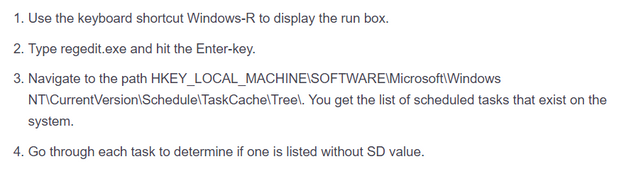
- Based on this blog - https://www.ghacks.net/2022/04/13/how-to-detect-the-windows-tarrask-malware-that-uses-a-bug-to-avoid...
- Use Sysmon to monitor registry changes. Which will generate EventCode=13 for any registry changes - https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventid=90013
- You can use https://splunkbase.splunk.com/app/5709/ Sysmon Add-on to collect and parse these logs.
I'm giving a solution based on this blog:
I would suggest also exploring the solution given by @Azeemering , as that will not require to install Sysmon.
I hope this helps!! Upvote/Karma would be appreciated!!!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@VatsalJagani Huge help. Big Thanks.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Modify your audit policy to identify Scheduled Tasks actions by enabling logging “TaskOperational” within Microsoft-Windows-TaskScheduler/Operational. Apply the recommended Microsoft audit policy settings suitable to your environment.
Enable and centralize the following Task Scheduler logs. Even if the tasks are ‘hidden’, these logs track key events relating to them that could lead you to discovering a well-hidden persistence mechanism
Event ID 4698 within the Security.evtx log
Microsoft-Windows-TaskScheduler/Operational.evtx log
The threat actors in this campaign used hidden scheduled tasks to maintain access to critical assets exposed to the internet by regularly re-establishing outbound communications with C&C infrastructure. Remain vigilant and monitor uncommon behavior of your outbound communications by ensuring that monitoring and alerting for these connections from these critical Tier 0 and Tier 1 assets is in place.