Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Different number of events same query
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have 2 servers that receive the logs through Syslog and through a universal forwarder I forward them to 2 indexers.
I have 2 search heads that are not in cluster mode, they are in "Standalone"
Only Splunk Enterprise is installed in one search head, and Splunk Enterprise and Splunk Enterprise Security are installed in the other.
For obvious reasons, they both have the peer pointing to both indexers.
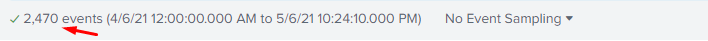
What makes me curious is why if I make a query of any type of Query SPL in the search head where Splunk ES is, it shows that it went to search more logs than in the search head where I only have Splunk.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @splunkcol,
there is no reason for the behavior you said.
the only question I can ask you is the following: what is the execution time range of the two searches?
try to set the same time range but always in the past, never using "until now" (latest = now).
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @splunkcol,
there is no reason for the behavior you said.
the only question I can ask you is the following: what is the execution time range of the two searches?
try to set the same time range but always in the past, never using "until now" (latest = now).
Ciao.
Giuseppe