Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Count for each ID depending on EXEC time
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
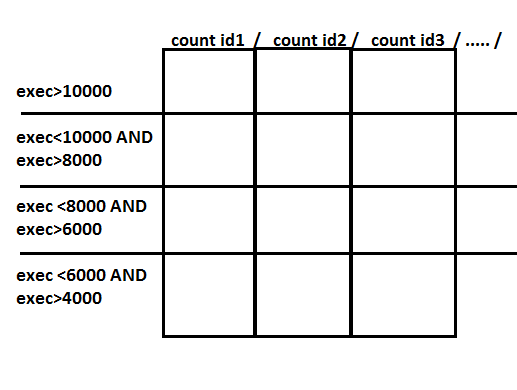
I'm searching a way to sort a number of events depending on the value of a field :
One event has a field EXEC, which is an execution time and an ID.
I want to count the number of events that has an exec > 10000, exec between 10000 AND 8000, ...
I was imagining it like this :
I'm searching at the moment with :
index=... exec>10000 | stats count as Events by id
Which return me the numbers of events that has an exec > 10000 for each id. Searching with some if condition but without any results .
Thanks for your help
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
You could use eval function:
... | eval exec_time=case(exec > 1000, ">1000", exec >=1000 AND exec < 8000, "1000-8000") | stats count by exec_time, id
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
You could use eval function:
... | eval exec_time=case(exec > 1000, ">1000", exec >=1000 AND exec < 8000, "1000-8000") | stats count by exec_time, id
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, it was exactly what i was looking for 🙂
I just remark that it's not really relevant to show the result on a graph... Seems that Splunk miss table 😛
I re-write my code if can help other users :
index=...
| eval exec_time=case(
exec <= 50, "<50",
exec >50 AND exec <=100, "50 - 100",
exec >100 AND exec <=200, "101 - 200",
exec >200 AND exec <=500, "201 - 500",
exec >500 AND exec <=2000, "501 - 2000")
| stats count by exec_time, id