Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Combining fields
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Combining fields
gagareg
Explorer
02-11-2020
05:20 AM
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
gcusello

SplunkTrust
02-13-2020
03:01 AM
Hi @gagareg,
in each event do you have only one value (to or from or user) or could you have in the same event more fields?
If you have only one field for event, you can use coalesce function:
| eval email=coalesce(to,from,user)
If instewad you surely have all the three fields in each event, you can use a solution like the one of @harsmarvania57
| eval email=to."--".from."--".user
if you could have more fields in the same event but you're not sure that there are always all the three fields, you have to add a value to the three fields when there's no value before the eval row:
| eval to=fillnull(to,"-"), from=fillnull(from,"-"), user=fillnull(user,"-")
| eval email=to."--".from."--".user
otherwise the eval command doesn't run.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
harsmarvania57
Ultra Champion
02-11-2020
05:36 AM
HI,
Try below query
<your base search> | eval new_field = field_1 . "--" . field_2 . "--" . field_3
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
gagareg
Explorer
02-13-2020
02:29 AM
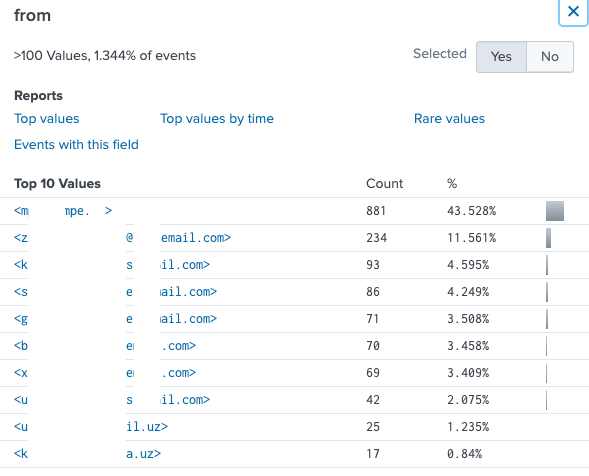
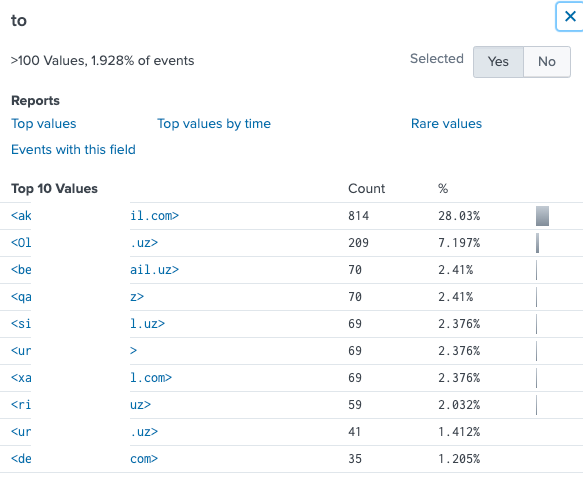
Unfortunately, it does not work.
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
[Puzzles] Solve, Learn, Repeat: Matching cron expressions
This puzzle (first published here) is based on matching timestamps to cron expressions.All the timestamps ...
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Why Splunk Customers Should Attend Cisco Live 2026 Las Vegas
Cisco Live 2026 is almost here, and this ...
Data Management Digest – May 2026
Welcome to the May 2026 edition of Data Management Digest!
As your trusted partner in data innovation, the ...