Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Brute Force Query Help
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Brute Force Query Help
alanzchan
Path Finder
08-03-2020
08:26 AM
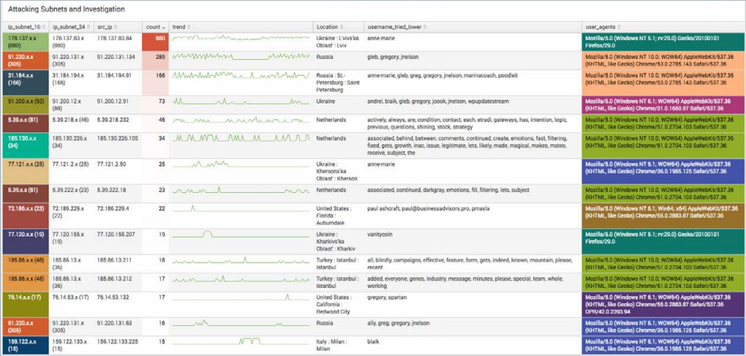
I am trying to mimic the table below. I have the count of the source IP, but how do I get the count of the respective subnets? In the example, they have it in the cell of each subnet value. Here is what I have so far:
index=xxxx sourcetype=xxxx "xxxx"
| eval ERROR_CODE=case((RC="200"), "Success", (RC="400"), "User Not Found",(RC="401") , "Bad Password",(RC="500"), "Internal Server Error")
| rex field=_raw "TCIP='(?<subnet_24>\d+\.\d+\.\d+)\.\d+"
| rex field=_raw "TCIP='(?<subnet_16>\d+\.\d+)\.\d+\.\d+"
| eval subnet_24 = subnet_24 +".x"
| eval subnet_16 = subnet_16 +".x.x"
| stats count(TCIP) by subnet_24 subnet_16 TCIP
Any help is appreciated!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
isoutamo

SplunkTrust
08-03-2020
09:30 AM
Hi
you should try eventstats instead of stats.
r. Ismo
Get Updates on the Splunk Community!
New Year, New Changes for Splunk Certifications
As we embrace a new year, we’re making a small but important update to the Splunk Certification ...
[Puzzles] Solve, Learn, Repeat: Unmerging HTML Tables
[Puzzles] Solve, Learn, Repeat: Unmerging HTML TablesFor a previous puzzle, I needed some sample data, and ...
Enterprise Security (ES) Essentials 8.3 is Now GA — Smarter Detections, Faster ...
As of today, Enterprise Security (ES) Essentials 8.3 is now generally available, helping SOC teams simplify ...