Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Are wildcards with tstats on accelerated data mode...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm running a search that is something like this:
| tstats values from datamodel=foo
When the datamodel is not accelerated, I get all my data.
When it is accelerated, no data is returned.
If i specify the fields with values(foo), values(bar)and so on, it works just fine.
Does anyone know if wildcards or returning all values at once isn't supposed to work if the datamodel is accelerated?
Any way to get around this?
Thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Forgot to close this one.
Splunk support said this isn't supported and won't be supported in the near future if anyone wonders.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Forgot to close this one.
Splunk support said this isn't supported and won't be supported in the near future if anyone wonders.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Goophy,
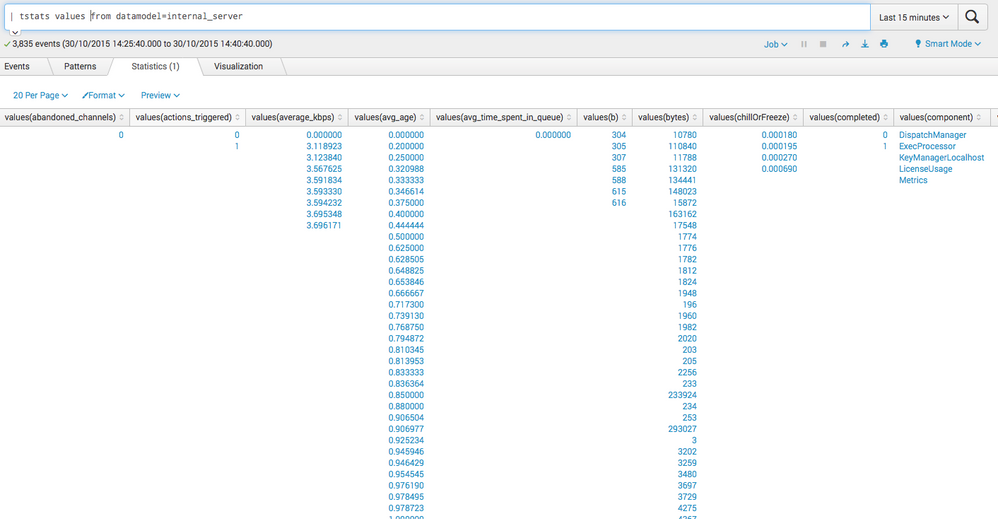
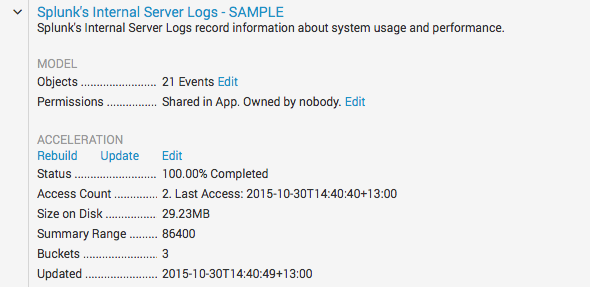
take this run everywhere command which just runs fine on the internal_server data model, which is accelerated in my case:
| tstats values from datamodel=internal_server
the result is this:
and as you can see it is accelerated:
So, to answer to answer your question: Yes, it is possible to use values on accelerated data models to return all values.
Maybe you hit some limit (haven't found anything on a quick search) and try to return too much values at once?
cheers, MuS
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you very much for the answer.
The acceleration puts things in TSIDX in 5-minute increments, so the last 15 minutes will always return something.
Can you try to search for yesterday or something?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sure, running this | tstats values from datamodel=internal_server where earliest=-1d@d latest=-0d@d returns this for me (Sorry for the ugly paste):
values(bytes) values(count) values(date_hour) values(date_mday) values(date_minute) values(date_month) values(date_second) values(date_wday) values(date_year) values(date_zone) values(digest) values(eventtype) values(file) values(host) values(ident) values(index) values(linecount) values(nodename) values(other) values(punct) values(req_time) values(root) values(search) values(server.acceleration.is_dm_acceleration) values(server.acceleration.is_not_dm_acceleration) values(server.acceleration.is_not_report_acceleration) values(server.acceleration.is_report_acceleration) values(server.clientip) values(server.is_acceleration) values(server.is_licenser) values(server.is_metrics) values(server.is_not_acceleration) values(server.is_not_licenser) values(server.is_not_metrics) values(server.is_not_scheduler) values(server.is_not_splunkdaccess) values(server.is_scheduler) values(server.is_splunkdaccess) values(server.licenser.is_daily_usage) values(server.licenser.is_not_daily_usage) values(server.licenser.is_not_pool_warnings) values(server.licenser.is_not_quota) values(server.licenser.is_not_slave_warn_summary) values(server.licenser.is_pool_warnings) values(server.licenser.is_quota) values(server.licenser.is_slave_warn_summary) values(server.method) values(server.metrics.is_Thruput) values(server.metrics.is_not_Thruput) values(server.metrics.is_not_pipeline) values(server.metrics.is_not_queue) values(server.metrics.is_not_systemwide_search_load_) values(server.metrics.is_not_user_search_load) values(server.metrics.is_pipeline) values(server.metrics.is_queue) values(server.metrics.is_systemwide_search_load_) values(server.metrics.is_user_search_load) values(server.scheduler.is_alerts) values(server.scheduler.is_not_alerts) values(server.scheduler.is_not_scheduled_reports) values(server.scheduler.is_not_summaryindexing) values(server.scheduler.is_scheduled_reports) values(server.scheduler.is_summaryindexing) values(server.spent) values(server.splunkdaccess.is_job_endpoint) values(server.splunkdaccess.is_not_job_endpoint) values(server.status) values(server.uri_path) values(server.uri_query) values(server.user) values(source) values(sourcetype) values(splunk_server) values(splunk_server_group) values(timeendpos) values(timestartpos) values(uri) values(version) values(with_new)
130333 131320 17548 3729 4367 60970 7123 77973 -1 500 15 30 56 october 28 29 friday 2015 780 1 splunkd-access admin default local searches tz user-prefs views indexer - _internal 1 server server.splunkdaccess - - - 11ms - - - 17ms - - - 1ms - - - 3ms - - - 6ms - - - 8ms - - - 9ms ..._-__[//:::._+]_"_///-_/."___-_-_-_ ..._-__[//:::._+]_"_///////_/."___-_-_-_ ..._-__[//:::._+]_"_//////?=&=-_/."___-_-_-_ ..._-__[//:::._+]_"_//////?=-_/."___-_-_-_ ..._-__[//:::._+]_"_/////?=&=%%%%&=_/."___-_-_-_ ..._-__[//:::._+]_"_////_/."___-_-_-_ ..._-__[//:::._+]_"_///?=%&=%&=-_/."___-_-_-_ 30/Oct/2015:15:56:28.979 +1300 30/Oct/2015:15:56:28.985 +1300 30/Oct/2015:15:56:28.998 +1300 30/Oct/2015:15:56:29.022 +1300 30/Oct/2015:15:56:29.043 +1300 30/Oct/2015:15:56:29.062 +1300 30/Oct/2015:15:56:29.080 +1300 30/Oct/2015:15:56:29.101 +1300 30/Oct/2015:15:56:29.121 +1300 30/Oct/2015:15:56:29.150 +1300 30/Oct/2015:15:56:29.208 +1300 services servicesNS disabled%3Dfalse is_visible%3D1%20AND%20disabled%3D0 0 1 1 0 127.0.0.1 0 0 0 1 1 1 1 0 0 1 0 1 1 1 1 0 0 0 GET 0 1 1 1 1 1 0 0 0 0 0 1 1 1 0 0 1 11 17 3 6 8 9 0 1 200 /services/apps/local /services/authentication/users/admin /services/data/user-prefs /services/search/timeparser/tz /servicesNS/admin/launcher/data/ui/nav/default /servicesNS/admin/launcher/data/ui/views /servicesNS/admin/launcher/saved/searches _with_new=1&search=is_visible%3D1%20AND%20disabled%3D0&count=500 count=-1 digest=1&count=-1 search=disabled%3Dfalse&search=visible%3Dtrue&count=-1 admin /opt/splunk/var/log/splunk/splunkd_access.log splunkd_access michael-VirtualBox dmc_group_deployment_server dmc_group_indexer dmc_group_kv_store dmc_group_license_master dmc_group_search_head 49 19 /services/apps/local?search=disabled%3Dfalse&search=visible%3Dtrue&count=-1 /services/authentication/users/admin /services/data/user-prefs /services/search/timeparser/tz /servicesNS/admin/launcher/data/ui/nav/default /servicesNS/admin/launcher/data/ui/views?count=-1 /servicesNS/admin/launcher/data/ui/views?digest=1&count=-1 /servicesNS/admin/launcher/saved/searches?_with_new=1&search=is_visible%3D1%20AND%20disabled%3D0&count=500 HTTP/1.0 1
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Awesome, thanks!
Then I know it's just something I'm doing.
Getting no results doing exactly the same as you on both fresh 6.2.0 and 6.3.0 installs.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this was useful and answered your question, please accept the answer - thx.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't want to tag it as answered yet as I still can't reproduce your results unfortunately.
Which version of Splunk do you use?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk 6.3
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is so weird.
I've ran the exact same search on fresh 6.3-installs on three different Debian and RHEL-servers.
No results. A simple count shows that there is data though.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you tried some different browsers too?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just tried Chrome, IE and Firefox.
No difference.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have a look at the job inspector and see what is reported there; running | tstats values from datamodel=internal_server over today returns for me this at top of the job inspector:
This search has completed and has returned 1 result by scanning 213,774 events in 0.377 seconds.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
"today" will always contain the last 5 minutes of data which is not accelerated, and that returns something.
If I run yesterday I get the standard:
This search has completed and found 371,510 matching events. However, the transforming commands in the highlighted portion of the following search:
| tstats values from datamodel=internal_server
over the time range:
02/11/2015 00:00:00.000 – 03/11/2015 00:00:00.000
generated no results. Possible solutions are to:
So there is data, but it seems like the accelerated DM just doesn't want to show fields not explicitly mentioned.