- Splunk Answers
- :
- Splunk Platform Products
- :
- Splunk Enterprise
- :
- Re: Event has no datetime at the beginning splits ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi there,
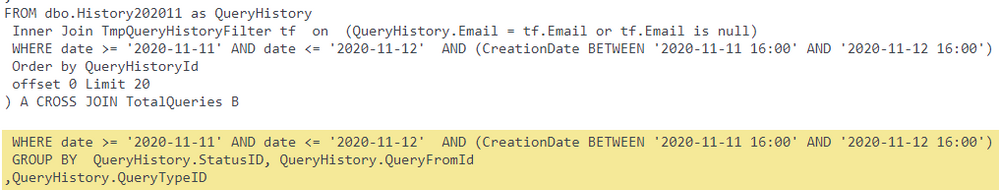
When reviewing Splunk events, some events display as below, it splits following text into two events; the second event has no datetime at the beginning, and the log is from log4net with datetime.
...
FROM dbo.History202011 as QueryHistory Inner Join TmpQueryHistoryFilter tf on (QueryHistory.Email = tf.Email or tf.Email is null) WHERE date >= '2020-11-11' AND date <= '2020-11-12' AND (CreationDate BETWEEN '2020-11-11 16:00' AND '2020-11-12 16:00') AND QueryTypeID IN (1,4) AND CompanyID = 42 Order by QueryHistoryId offset 0 Limit 20 ) A CROSS JOIN TotalQueries B
WHERE date >= '2020-11-11' AND date <= '2020-11-12' AND (CreationDate BETWEEN '2020-11-11 16:00' AND '2020-11-12 16:00') AND QueryTypeID IN (1,4) AND CompanyID = 1000 GROUP BY QueryHistory.StatusID, QueryHistory.QueryFromId ,QueryHistory.QueryTypeID ,CASE WHEN QueryHistory.EAScore >=900 THEN 1...
Any thought?
Thanks,
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks @richgalloway but most events are splitting correctly with the date in single line.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What are the props.conf settings for that sourcetype?
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks richgalloway, looks we have no such props.conf setting.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's likely to be the problem. Every sourcetype onboarded should have a stanza in a props.conf file. Without it, Splunk is just guessing about your data and could be guessing wrong (as in this case).
Each stanza in props.conf should at least specify these settings: LINE_BREAKER, TIME_PREFIX, TIME_FORMAT, MAX_TIMESTAMP_LOOKAHEAD, SHOULD_LINEMERGE, TRUNCATE.
If this reply helps you, Karma would be appreciated.
