Join the Conversation
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- Maxmind Threat Intelligence Database is not downlo...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maxmind Threat Intelligence Database is not downloading
Hi there, I noticed that the URL path for the MaxMind ASN Database has changed on, to another path, and the siem can research for the file.
When I tried to put the new path, I realize that the zip file has a folder with two files and it is unreadable for the Splunk
¿Anyone has the same problem? ¿Is there another way to update the threat intelligence with IP Geolocation?
Best Regards,
Jose León
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Anyone know if this has been fixed yet?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
There are several Splunkbase Apps around this, with one of the latest being the : ASN Lookup Generator
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Where are you using the ASN file? Splunk ships with GeoLite2-City.mmdb, which is all that you should need to update.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The ASN file is used in ES in the below lookup Gens
Threat - ASN CIDR Matches - Lookup Gen
Threat - ASN IPv6 CIDR Matches - Lookup Gen
Threat - ASN String Matches - Lookup Gen
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Jose,
This has been identified as an issue to be addressed under SOLNESS-17731
- " Name and location of the MaxMind GeoIP database has changed "
At present others are using the workaround of extracting the downloaded zip folder to a hosted web server or e.g. github repository.
Hope it helps,
Cheers,
Matt - Splunk.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @mdillon_splunk,
There is now a requirement that we and other users first obtain a free license key from MaxMind (https://blog.maxmind.com/2019/12/18/significant-changes-to-accessing-and-using-geolite2-databases/) and update the link to take this into account such that the URL becomes "https://download.maxmind.com/app/geoip_download?edition_id=GeoLite2-ASN-CSV&license_key=INSERT_LICEN...".
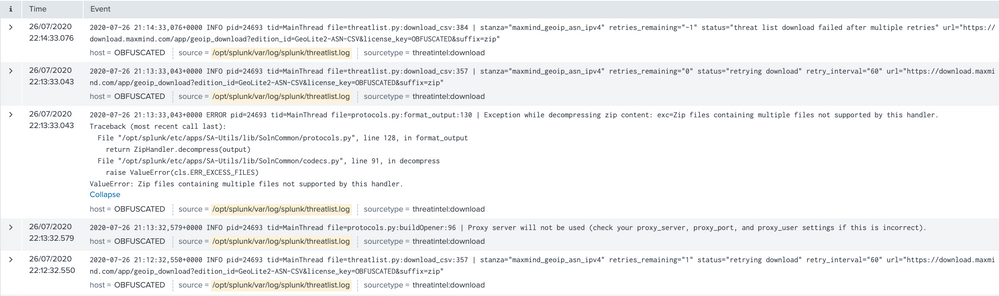
The reason I'm raising this after quite some time since the last post on this thread is that I'm wondering whether "SOLNESS-17731" is also planning to take into account that the backend Python code that Splunk uses for this functionality (called "threatlist.py" & "protocols.py") seems to currently be unable to process archives which have multiple files within, as the screenshot below from my experimentation shows:
The problem here is that MaxMind currently doesn't provide these files except as part of a ZIP or TAR.GZ archive with the following multi-file structure:
Folder: GeoLite2-ASN-CSV_20200728
File underneath: GeoLite2-ASN-Blocks-IPv4.csv
File underneath: COPYRIGHT.txt
File underneath: GeoLite2-ASN-Blocks-IPv6.csv
File underneath: LICENSE.txt
Thus, it would be ideal if we could somehow specify a configuration parameter when setting up the input like "File location: GeoLite2-ASN-CSV_YYYYmmdd/GeoLite2-ASN-Blocks-IPv4.csv" so that we can select which file Splunk will parse out of the archive.
We have a use case which relies on these CIDR IP <> ASN mappings so it would be great to get an update on whether something like the above has been considered as part of "SOLNESS-17731"; also could you please let me know if this should rather be raised as a Splunk Idea instead.
Many thanks !
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @rragazan
The issue should now be addressed with Enterprise Security 6.2.0
https://docs.splunk.com/Documentation/ES/6.2.0/RN/FixedIssues
SOLNESS-22110 - Threat Intelligence: Maxmind ASN database can no longer be consumed