Are you a member of the Splunk Community?
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- How to find the source of excessive failed logins ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to find the source of excessive failed logins (bruteforce)?
We see there are 40,000 failed login attempts to a DC on our network but are unable to verify the source (IP) using Splunk. Assuming we are collecting all the necessary data, what should we search for to find the culprit?
We have ES and the indicators are consistent with a brute force attack.
Here is what we run to find those results.
| from datamodel:"Authentication"."Failed_Authentication" | search src="companydomain.com" | stats count by user | sort - count
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Depending on authentication load, and given this is a DC, this could be normal, it depends.
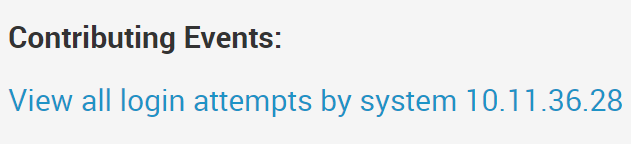
You could try selecting this link from your notable-event (which you might have already). Ensure your assets.csv correctly reflects reality, with both IPs and DNS/Hostnames, should make your ES experience better.
Otherwise you could remove "| search src="companydomain.com" from the search and look at everything that is failing authentication to deduce what's happening.
Cheers.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
use iplocation commmand