Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Enterprise Security
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Premium Solutions
- :
- Splunk Enterprise Security
- :
- How to create notable manually with selected times...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to create notable manually with selected timestamp?
bluewizard
Explorer
05-29-2023
09:05 PM
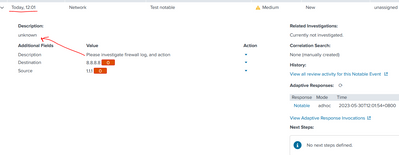
| stats count
| eval _time="1685158808"
| eval rule_title="Test notable"
| eval security_domain="Network"
| eval urgency="Medium"
| eval rule_name="Test rule"
| eval dest="8.8.8.8"
| eval src="1.1.1"
| eval desc="Please investigate firewall log, and action"
| sendalert notable param.mapfields=_time,desc,rule_id,rule_name,nes_fields,drilldown_name,drilldown_search,governance,control,default_owner,drilldown_earliest_offset,drilldown_latest_offset,next_steps,investigation_profiles,extract_artifacts,recommended_actions
Is it possible to use a timestamp to change the notable creation date time? it is creating notable everytime i hit search with the above query.`
Additionally how do i move my description from below to the above description?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
johnlee2327
Explorer
10-22-2024
09:02 PM
You can use "rule_description" as the field for the above description.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
meetmshah

SplunkTrust
07-17-2023
11:38 PM
AFAIK, The notable time is the time when the event gets triggered and indexed (and not _time from the events). However, I have heard that there is a feature in the upcoming version of ES where we can select notable time.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
bluewizard
Explorer
05-29-2023
11:15 PM
is this technically possible, or everytime i run sendalert notable it will create a notable with time now?
Get Updates on the Splunk Community!
[Puzzles] Solve, Learn, Repeat: Reprocessing XML into Fixed-Length Events
This challenge was first posted on Slack #puzzles channelFor a previous puzzle, I needed a set of fixed-length ...
Data Management Digest – December 2025
Welcome to the December edition of Data Management Digest!
As we continue our journey of data innovation, the ...
Index This | What is broken 80% of the time by February?
December 2025 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with this ...