- Splunk Answers
- :
- Splunk Premium Solutions
- :
- Security Premium Solutions
- :
- Splunk Enterprise Security
- :
- Re: Different Search Results From Two Macros With ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Different Search Results From Two Macros With Same Contents
Hello everyone. I'm looking for some assistance with a problem where I get differing search results from what should be the same search.
Backstory
I’m testing changes to the “ESCU - Malicious PowerShell Process - Execution Policy Bypass – Rule” so that I can filter out known PowerShell events.
Using the same search head, user, date and time range, and what should be two identical macros, I get different search results.
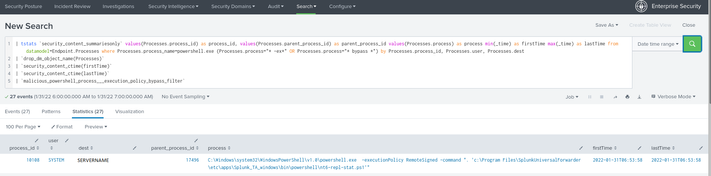
The original search uses this macro: “malicious_powershell_process___execution_policy_bypass_filter”
The original search is:
| tstats `security_content_summariesonly` values(Processes.process_id) as process_id, values(Processes.parent_process_id) as parent_process_id values(Processes.process) as process min(_time) as firstTime max(_time) as lastTime from datamodel=Endpoint.Processes where Processes.process_name=powershell.exe (Processes.process="* -ex*" OR Processes.process="* bypass *") by Processes.process_id, Processes.user, Processes.dest
| `drop_dm_object_name(Processes)`
| `security_content_ctime(firstTime)`
| `security_content_ctime(lastTime)`
| `malicious_powershell_process___execution_policy_bypass_filter`
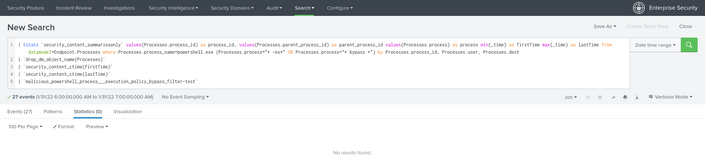
The test search uses this macro: “malicious_powershell_process___execution_policy_bypass_filter-test”
The test search is:
| tstats `security_content_summariesonly` values(Processes.process_id) as process_id, values(Processes.parent_process_id) as parent_process_id values(Processes.process) as process min(_time) as firstTime max(_time) as lastTime from datamodel=Endpoint.Processes where Processes.process_name=powershell.exe (Processes.process="* -ex*" OR Processes.process="* bypass *") by Processes.process_id, Processes.user, Processes.dest
| `drop_dm_object_name(Processes)`
| `security_content_ctime(firstTime)`
| `security_content_ctime(lastTime)`
| `malicious_powershell_process___execution_policy_bypass_filter-test`
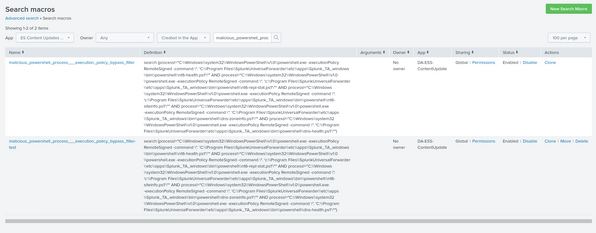
Both macros contain the same content to exclude Splunk Universal Forwarder PowerShell scripts:
search (process!="C:\\Windows\\system32\\WindowsPowerShell\\v1.0\\powershell.exe -executionPolicy RemoteSigned -command \". 'C:\\Program Files\\SplunkUniversalForwarder\\etc\\apps\\Splunk_TA_windows\\bin\\powershell\\nt6-health.ps1'\"" AND process!="C:\\Windows\\system32\\WindowsPowerShell\\v1.0\\powershell.exe -executionPolicy RemoteSigned -command \". 'c:\\Program Files\\SplunkUniversalForwarder\\etc\\apps\\Splunk_TA_windows\\bin\\powershell\\nt6-repl-stat.ps1'\"" AND process!="C:\\Windows\\system32\\WindowsPowerShell\\v1.0\\powershell.exe -executionPolicy RemoteSigned -command \". 'c:\\Program Files\\SplunkUniversalForwarder\\etc\\apps\\Splunk_TA_windows\\bin\\powershell\\nt6-siteinfo.ps1'\"" AND process!="C:\\Windows\\system32\\WindowsPowerShell\\v1.0\\powershell.exe -executionPolicy RemoteSigned -command \". 'C:\\Program Files\\SplunkUniversalForwarder\\etc\\apps\\Splunk_TA_windows\\bin\\powershell\\dns-zoneinfo.ps1'\"" AND process!="C:\\Windows\\system32\\WindowsPowerShell\\v1.0\\powershell.exe -executionPolicy RemoteSigned -command \". 'C:\\Program Files\\SplunkUniversalForwarder\\etc\\apps\\Splunk_TA_windows\\bin\\powershell\\dns-health.ps1'\"")
When I run both searches I get different results and I’m unsure why. The macro appended -test works fine. When I copy its contents to the original macro, that search does not seem to use the new contents.
I made these changes last week and today get the same results.
Any ideas as to what might be causing this?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you expand the macros (<ctrl><shift>E) do they expand as you would expect?
I have noticed that sometimes "updated" macros are not always updated in a timely manner, but I haven't figured out when and why this is - usually I keep retrying the update until it works. Sorry, that that is not much help.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Seems like it was a copy / paste oddity. I edited the macro again and copied / pasted the text back in. It works as expected now.
Perhaps there was some extra hidden characters that were causing an issue.
Thanks for the help.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reply. Sadly I'm using AWS Workspaces Linux and <ctrl><shift>E doesn't work for some reason. Just prints the e character.