Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Admin Other
- :
- Security
- :
- Windows: Unknown User Name or Bad Password
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi.
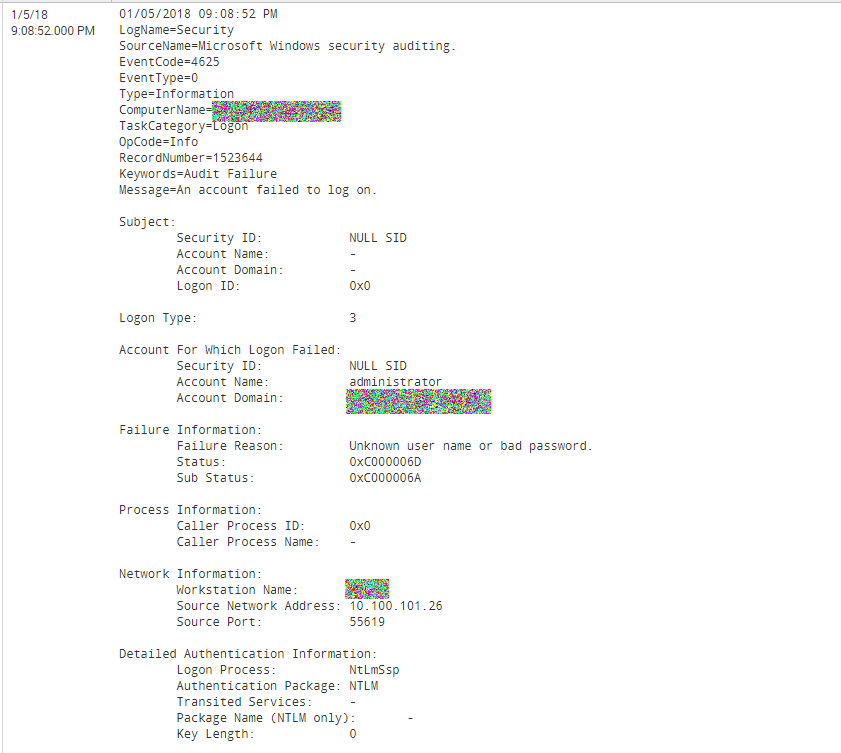
How can I distinguish events with Authentication when «Unknown User Name» and when «Bad Password»?
Ping me if you need more information 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
At first, I was going to think of a complicated option, assuming an option where you have a domain environment, you could use SA-ldapsearch to take the username and lookup and see if it exists in the domain.
But a better solution is much easier. You see the Failure Status and Substatus codes? Build a lookup for those... they come out of ntstatus.h. In particular 0xC0000064 means there is no such user, and 0xC000006A means wrong password.
Code List: https://msdn.microsoft.com/en-us/library/cc704588.aspx
Microsoft Windows Vista Security forum question: https://answers.microsoft.com/en-us/windows/forum/windows_vista-security/where-can-i-find-the-full-l...
You can also do some googling for event code 4625 and see what others have to say about it.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
At first, I was going to think of a complicated option, assuming an option where you have a domain environment, you could use SA-ldapsearch to take the username and lookup and see if it exists in the domain.
But a better solution is much easier. You see the Failure Status and Substatus codes? Build a lookup for those... they come out of ntstatus.h. In particular 0xC0000064 means there is no such user, and 0xC000006A means wrong password.
Code List: https://msdn.microsoft.com/en-us/library/cc704588.aspx
Microsoft Windows Vista Security forum question: https://answers.microsoft.com/en-us/windows/forum/windows_vista-security/where-can-i-find-the-full-l...
You can also do some googling for event code 4625 and see what others have to say about it.