Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- What to do when json field conflicts with Splunk m...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What to do when json field conflicts with Splunk metadata?
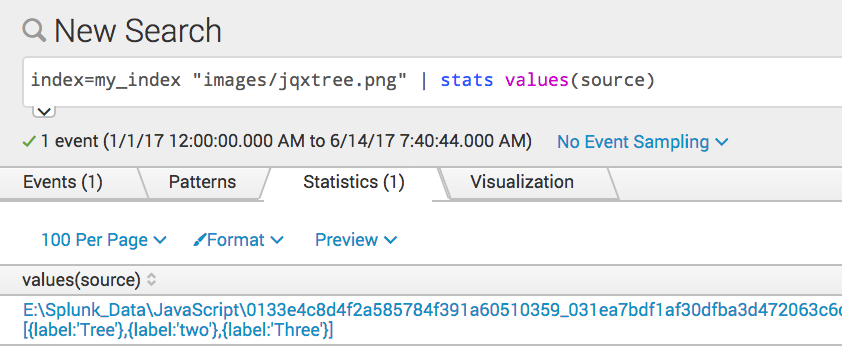
A user is reporting that their indexed json data has a 'source' key that is being extracted.
"source": "[{label:'Tree'},{label:'two'},{label:'Three'}]",
When they search their data, they see:
They'd like the original source kept intact. Is there a transforms that I can add to my indexers to rename ONLY the json source?
The raw json looks like: [ snipped ]
"toggleMode":"click",
"_toggleMode": {
"desc": "Gets or sets user interaction used for expanding or collapsing any item.",
"type": "enum",
"keys": ["click","dblclick"],
"values": ["click","dblclick"]
},
*"source": "[{label:'Tree'},{label:'two'},{label:'Three'}]",**
"_source": {
"desc": "Sets the initial contents. Easier to do at runtime.",
"type": "css",
"language": "JavaScript"
},*
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
transforms.conf
[change_source]
REGEX = "source":\s"[(\S+)]
FORMAT = source::$1
DEST_KEY = MetaData:Source