Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Splunk receive log question
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk receive log question
Dear all,
I am trying to use third party tools to centralize all the log and forward the log to Splunk. Because of some reason, I need to use this third tool instead of Splunk forwarder.
I success to forward the log to Splunk. However, I find there is two host in the log. one of the IP is forwarder IP.
Example
host: 1.1.1.1 <- forwarder IP
2.2.2.2 <- real IP
May I know is it possible to remove the forwarder IP from the log through Splunk?
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
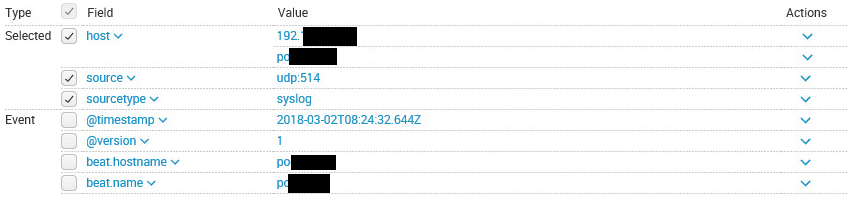
I use logstash to forward log to splunk through udp 514. sourcetype is syslog. the following is the sample log
According to the log, in the host field, there is two value. the upper one is forwarder, the other one is original host ip. All the event have this problem.
So i want to know is it possible to remove the forwarder address through splunk
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think you'll need to provide a bit more detail on how you get the data in (share relevant parts from your inputs.conf for example, what sourcetype(s) is/are used...) and what the data really looks like before anyone can provide a good answer to that question.
Is the host field multi valued, or do some events get the forwarder IP and other events the original host IP?