- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Splunk Security Essentials integration with Forcep...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk Security Essentials integration with Forcepoint app.
Hello,
I've been trying to get data in SSE, but somehow I can't. The setup is the following - Installed Splunk Enterprise, Universal Forwarder, Forecpoint app, Syslog-ng(for receiving the logs, which i monitor with the UF) and Splunk Security Essentials.
I've tried different things with the demo data but when I'm trying to do anything with the live data i hit the wall. I've tried to follow https://docs.splunk.com/Documentation/SSE/3.4.0/Install/ConfigureSSE these instructions, but they seem unclear and somehow inaccurate(For example in the chapter for getting data in - Configure the products you have in your environment with the Data Inventory dashboard. When I browse in the web interface there is no option to "2.b.Click Manually Configure to manually enter your data.") .
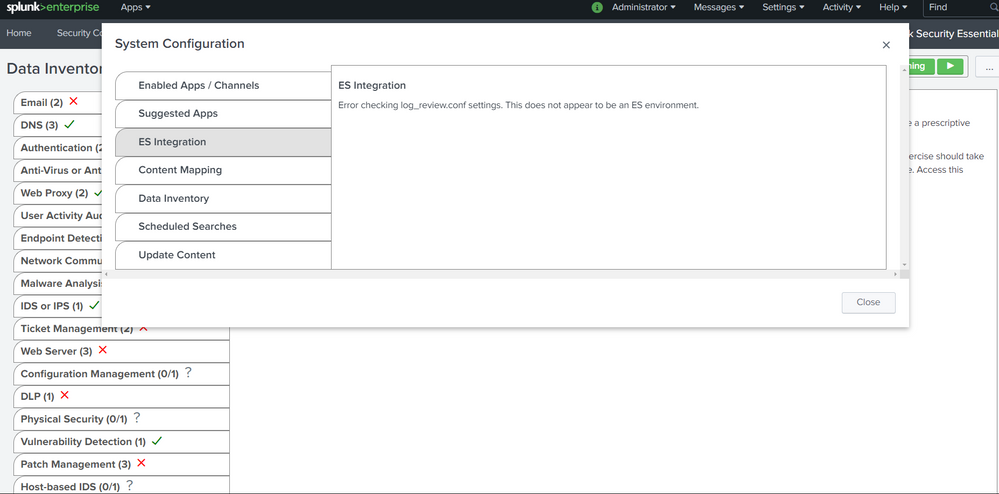
The first thing I've noticed was that this error for the ES Integration was thrown, for which i didn't find any information.
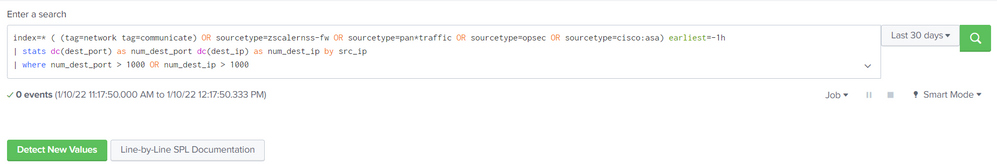
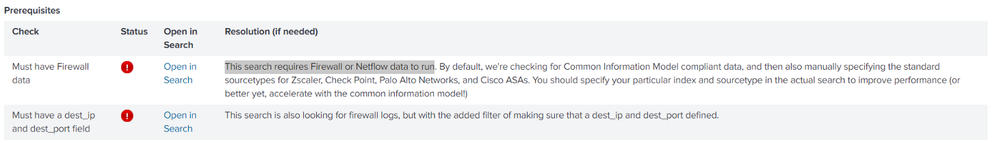
When I open any use cases and for example "Basic Scanning", the sourcetype and index for forcepoint (index="forcepoint", sourcetype="next-generation-firewall") are missing by default. Are there any ways to add it automatically for all the use cases?
I've already have logs monitored by the indexer forwarded by the Forcepoint which are displayed in the Splunk Search and Reporting and Forcepoint App.
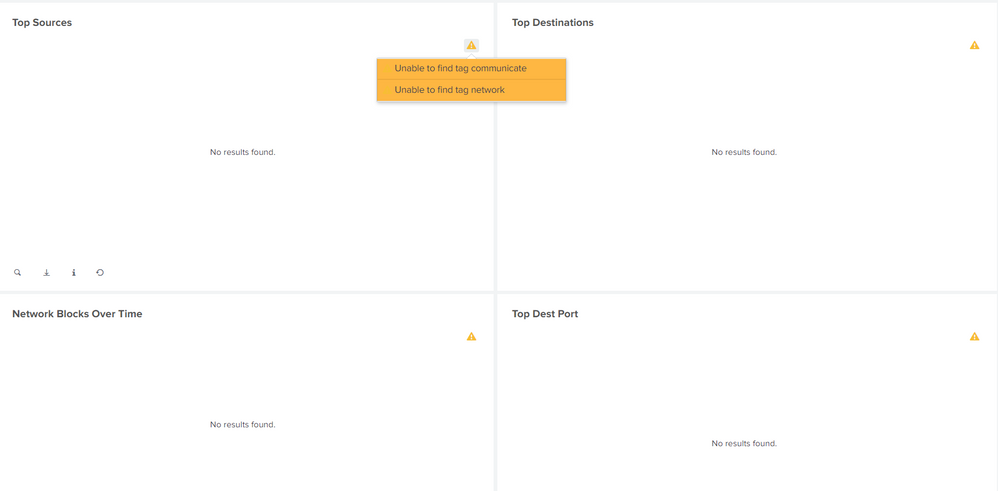
Even if i change the index and sourcetype in the enter a search field I still get these results. Can you give me any info on the tags, like what are they and what are they used for?
Any guides or tips will be highly appreciated, thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any time you find a Splunk document to be lacking, submit feedback on that docs page. The Documentation team is great about updating docs in response to user feedback.
The message in the first screenshot indicates you do not have Splunk Enterprise Security installed. To resolve it, buy and install ES.
The use cases in SSE are built using somewhat generic SPL, but should always be examined and updated before deploying it in a real environment. For example, many use cases use "index=*", which should never be allowed in a Production system. Also, some examples use products you may not have so you'll need to modify those examples to use data from your products.
The tags shown in the last screenshot come with the Splunk Common Information Model (CIM) app, IIRC.
IMO, the Splunk Security Essentials app should not be used as a SOC tool, but as a way to learn what you can do with Splunk to solve SOC use cases. Use SSE to see what is possible using your data and what data you need to solve other use cases, but take those examples and implement them in your own app.
If this reply helps you, Karma would be appreciated.