Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: Import registry (regedit) data into Splunk.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Import registry (regedit) data into Splunk.
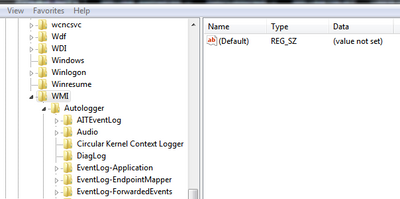
What i would like to do is to take this form from regedit,
and splash it into Splunk.
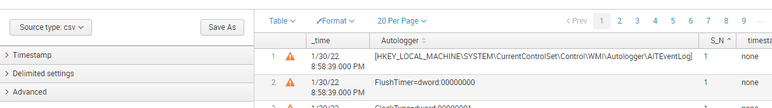
I have exported data from \WMI\Autologger level, put a sort of serial number at each "line" and tried to convert it into .csv
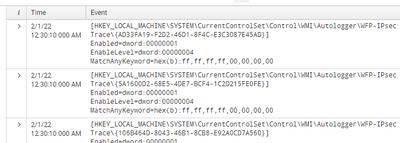
When i Add Data and do a index once file, i get this
My main request is to be able to do a table with all that information spreaded on multiple columns. Would help me alot.
What can i do or moddify in my file so splunk could know what is what and what is going where.
Should i leave it like this, or woud be better to be multiple info in the same "row"?
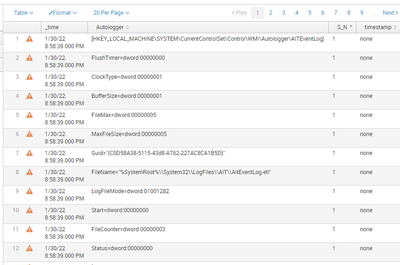
Instead of this:
I'm thinking more about at this example:
How can i tell Splunk to ket data like this?
Thanks for anyone who reads this time.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is not clear whether the S_N changes for each Key/set of values
Assuming it doesn't and you are working with just the Autologger values, you could try something like this
| rex field=Autologger "^(?<sectionKey>\[.*\])$"
| streamstats latest(sectionKey) as sectionKey
| rex field=Autologger "(?<_name>\w+)=(?<_value>.*)"
| eval {_name}=_value
| fields - _name _value Autologger
| stats values(*) as * by sectionKey
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
S/N or S_N, how Splunk rename it, is just a name for serial number that i put it there, in the hope that Splunk would know to get all data of a key and make it into one cassette/cell. What is 1 is a key in registry. Keep in mind that i didn't imported data in Splunk just yet. I'm looking for alteranatives as just how i could import it in Splunk so i can better understand it.
Your code, i assume, would work in search field, right?
What i was asking was how could i import it better so i can work with it better.
My main questions are:
1. If i put a kind of serial number to all keys, Splunk would know what is what and where it needs to go?
Example:
This is the original file
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\WMI\Autologger\AITEventLog]
"FlushTimer"=dword:00000000
"ClockType"=dword:00000001
"BufferSize"=dword:00000001
"FileMax"=dword:00000005
"MaxFileSize"=dword:00000005
"Guid"="{C0D58A38-5115-43d8-A762-227AC8CA1B5D}"
"FileName"="%SystemRoot%\\System32\\LogFiles\\AIT\\AitEventLog.etl"
"LogFileMode"=dword:01001282
"Start"=dword:00000000
"FileCounter"=dword:00000003
"Status"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\WMI\Autologger\AITEventLog\{6ADDABF4-8C54-4eab-BF4F-FBEF61B62EB0}]
"Enabled"=dword:00000001
"MatchAnyKeyword"=hex(b):00,00,00,00,00,00,00,00
"Status"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\WMI\Autologger\Audio]
"GUID"="{15BC788A-6A38-4D79-8773-B53FDFB84D79}"
"FileName"=""
"MaxFileSize"=dword:00000002
"LogFileMode"=dword:10008400
"Start"=dword:00000000
"ClockType"=dword:00000002
"Status"=dword:00000000
This would be the serialized file
1,[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\WMI\Autologger\AITEventLog]
1,FlushTimer=dword:00000000
1,ClockType=dword:00000001
1,BufferSize=dword:00000001
1,FileMax=dword:00000005
1,MaxFileSize=dword:00000005
1,"Guid=""{C0D58A38-5115-43d8-A762-227AC8CA1B5D}"""
1,"FileName=""%SystemRoot%\\System32\\LogFiles\\AIT\\AitEventLog.etl"""
1,LogFileMode=dword:01001282
1,Start=dword:00000000
1,FileCounter=dword:00000003
1,Status=dword:00000000
,
2,[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\WMI\Autologger\AITEventLog\{6ADDABF4-8C54-4eab-BF4F-FBEF61B62EB0}]
2,Enabled=dword:00000001
2,"MatchAnyKeyword=hex(b):00,00,00,00,00,00,00,00"
2,Status=dword:00000000
,
3,[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\WMI\Autologger\Audio]
3,"GUID=""{15BC788A-6A38-4D79-8773-B53FDFB84D79}"""
3,"FileName="""""
3,MaxFileSize=dword:00000002
3,LogFileMode=dword:10008400
3,Start=dword:00000000
3,ClockType=dword:00000002
3,Status=dword:00000000
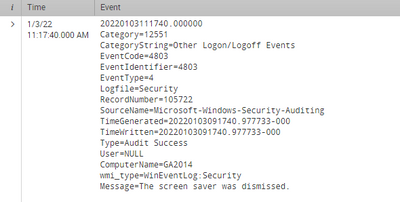
2 If i want to, can i, could i make, let's say "...\AITEventLog]" look more like this type of records?
20220103111740.000000
Category=12551
CategoryString=Other Logon/Logoff Events
EventCode=4803
EventIdentifier=4803
EventType=4
Logfile=Security
RecordNumber=105722
SourceName=Microsoft-Windows-Security-Auditing
TimeGenerated=20220103091740.977733-000
TimeWritten=20220103091740.977733-000
Type=Audit Success
User=NULL
ComputerName=XXXXXX
wmi_type=WinEventLog:Security
Message=The screen saver was dismissed.And how could i do that? How can i tell Splunk to get data from that file and show i to me like this?
Thank you for your time.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It depends on what you are trying to do with the data and how often it changes.
If it doesn't change very much or often, you could load it as a csv file but then you might want to do the transformation I outlined to get all the fields for an event (registry key) on a single line.
If if changes more frequently, and you want to keep previous versions of the file in splunk, you might want to consider ingesting each new version from a new source/file.
Ingesting as a file might allow you to join the lines for a single key into a single event as @PickleRick alluded to, although having ingested and indexed it, it is in the index until it is deleted or expires, whereas you could delete and reload the csv if you only want a single copy, but that is more manual effort.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In this case you can separate events with an empty line. Use two line ends as the event breaker.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Idea (untested) from the top of my head - you could use ^\[ as an event breaker. If I remember correctly though, it will consume the opening square parenthesis so the event will be a bit "ugly".
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Done, i have figure it out. Thank you.
Something like this i was looking for. If it is correct? I don't know :))
But! Still is something to work with.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Where it should go this ^\[ as it doesn't do anything ...