Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- How to disable logging
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to disable logging
We are currently running Splunk Enterprise, on-prem on a Linux VM and have a search head, with several forwarders.
How can we maintain the search functionality for historical log data, but stop/disable logging of any new data, either a blanket stop for all hosts/forwarders, or individually?
I think this can be done in the .conf file somehow? Is there an easier way to do this?
Our Splunk System Admin has left our company and I am trying to get up to speed on how this would be done.
Thanks,
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello
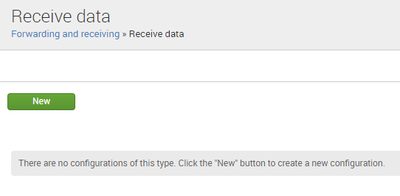
When I look at my Master server, as well as the individual server, within Settings > Forwarding and Receiving > Receiving, nothing is listed. It's blank.
However, within the Master server, under Forwarding, I see the forwarding to our 3 servers, see image below.
When I navigate to Receiving, it's blank, as seen below.
How would I disable receiving then, within the indexers themselves?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Jnewman28,
have you an Indexer Cluster or a stand-alone server?
Viewing your screenshot I see that you're in the Master Node, infact it sends its internal logs to the three Indexers you have (splunk-idx-c1.hfelocal.corp, etc...) but it hasn't an active receiving because Master Node doesn't receive logs.
You have to disable receiving in your Indexers, not in Master Node.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
here is good instructions how to figure out what you have in your splunk installations https://docs.splunk.com/Documentation/Splunk/8.2.2/InheritedDeployment/Introduction
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@gcusello Thank you. When I went to this page, there are no configurations listed.
When I click "New", it asks "Listen on this port *"
What information needs to be entered to disable receiving? I was hoping there would be a simple On/Off receive function. I want to know how to do this end to end, but not actually perform this now.
Thanks for your input for a Splunk newbie.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Jnewman28,
one step back:
which kind of logs are you receiving?
If you have forwarders that send logs to the Indexers, you have to disable receiving in all indexers following the procedure I described.
So if you don't find any receiving configurations, maybe you're watching in the wrong server, are they Indexers?
If you have other kinds of logs you have to disable them one by one always on Indexers.
In other words, have a you a perimeter that maps your data flows?
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Thanks for your reply, I didn't see your question.
We recieve application logs from several forwarders. We have a clustered environment with 1 Master server and 3 indexers.
See attached screenshot for the 3 indexers that appear within "Forward Data". Our "Receive Data" link is blank.
Which sub page should I be going into to make the changes to disable log forwarding/receiving? I'm unclear if I should be disabling forwarding or receiving at this point.
Thanks for your patience.
Jacob
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Jnewman28,
No problem, it's a pleasure to help you.
To receive logs from forwarders, you should have enabled receiving [Settings - Forwarding and receiving -- Receiving] in all your 3 Indexers, something like this:
And you have to disable it to stop Forwarders' logs without stopping each Forwarder, otherwise you have to stop each Forwarder.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Jnewman28,
you have to disable the Receiving from all the Forwarders [Settings -- Forwarding and Receiving -- Receiving].
Then, if you have other inputs on the Indexers (network, HEC, WMI, etc...), you have to disable them one by one.
In this way you'll be able to search all the events from the retention date to the block date until you'll have a Splunk license.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gcusello
Thanks for your quick reply.
Where can I locate my indexers so I can disable receiving within them?
Is disabling within the indexers done in the Splunk UI?
I really appreciate your help.
Thanks,
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Jnewman28,
You should be able to access via GUI to your Indexers.
You can find the Receiving configuration at [Settings -- Forwarding and Receiving -- Receiving].
You indexers are called splunk-idx-c1.hfelocal.corp, splunk-idx-c2.hfelocal.corp, splunk-idx-c3.hfelocal.corp.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reply. If we eventually downgraded to the free license sometime in the future, would that prevent us in any way from accessing the historical log data through searching in the Splunk UI?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Jnewman28,
ablolutely not: with the Free license you'll be able to access all the data you have, but with limited function (e.g. you will not have the login).
Ciao.
Giuseppe