Are you a member of the Splunk Community?
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: Can you help me with my search to extract and ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you help me with my search to extract and stats count a JSON field using Splunk?
Hi ,
I want a Splunk query to extract and stats count filed from JSON msg body.
For e.g:
index=abc org_name="JBL" AND app_name="contract-rules" AND space_name=Production msg="LoggingService = ContractRule, ContractId, Type = *, Status = Success"|stats count as Success by Src,Type
app_id: 6a878fd5-540e-4a28-b7ae-970e8a91b74e
app_name: contract-rules
org_name: JBL
space_name: Production
message_type: OUT
**msg: 2018-10-04 18:27:38.302 INFO [bill-cntct-rules-v0,57a307b46ae1593b,57a307b46ae1593b,true] 18 --- [nio-8080-exec-4] c.u.f.b.c.service.CntctRuleService : LoggingService = ContractRule, ContractId = H235678, Type = ASC, Src = JBL, Status = Success**
origin: rep
source_instance: 2
source_type: APP/PROC/WEB
timestamp: 1538677658302837000
}
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Attached snippet . Current SQL allows me to result the count using stats of fields out of msg body.
Below is my msg body
msg: 2018-10-05 18:01:50.429 INFO [billing-contract-rules-v0,873b26f593081fd6,873b26f593081fd6,true] 19 --- [nio-8080-exec-3] c.u.f.b.c.service.ContractRuleService : LoggingService = ContractRule, ContractId = MY66610, Type = CAS, Src = BMX, Status = Success
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
so if u put the part of my sample search below without the field=msg just prior to your pupe stats portuon it should work.
|rex “Type\s+\=\s+(?P<Type>[^\,]+)\,\s+Src\s+\=\s+(?P<Src>[^\,]+)\,”
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
any luck?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This assumes that you have msg extracted, if not drop field=msg.
index=abc org_name="JBL" AND app_name="contract-rules" AND space_name=Production msg="LoggingService = ContractRule, ContractId, Type = , Status = Success" |rex field=msg “Type\s+\=\s+(?P<Type>[^\,]+)\,\s+Src\s+\=\s+(?P<Src>[^\,]+)\,” |stats count as Success by Src,Type
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did not work
Error in 'SearchParser': Missing a search command before '^'. Error at position '228' of search query 'search index=abc org_name="JBL" c...{snipped} {errorcontext = (?P[^\,]+)\,\s+}'.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hmm seems to be something with the search syntax. Can you add a screenshot?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
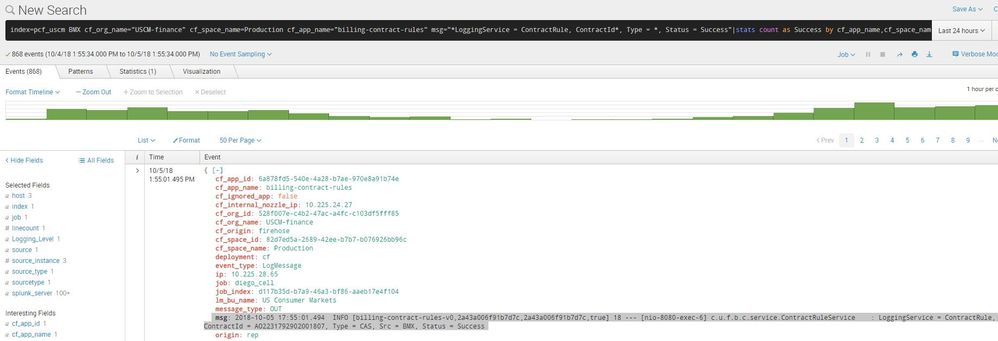
Attached snippet
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Basically I want to extract Src, Type and same want to use in my stats count
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you clarify what you want extracted from the message body? The rex command would likely work well but need to clarify your goal(s).