Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Adapt search filter to a query
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
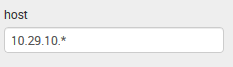
i need to insert IP addresses here
coded as follow:
<input type="text" token="host" searchWhenChanged="false">
<default>*</default>
</input>
to be applied to:
| pivot Cisco_IOS_Event Device last(hostname) AS "Hostname" last(site_id) AS "Site ID" last(model) AS "Model" last(serial_number) AS "Serial number" count(Device) AS "Count of events" SPLITROW host AS host
and many others panels. I should need to understand where to insert in panel's queries the referens to search-box posted above.
E.g.:
in this query, search-box works fine and it outputs me only IPs int 10..29.10.x subnet:
| pivot Cisco_IOS_Event Cisco_IOS_Event count(Cisco_IOS_Event) AS "Count of Cisco IOS Event" SPLITROW host AS host SPLITCOL severity_id_and_name FILTER host is "$host$" SORT 500 host ROWSUMMARY 0 COLSUMMARY 0 NUMCOLS 100 SHOWOTHER 1 | sort -"0 - emergency", -"1 - alert", -"2 - critical", -"3 - error", -"4 - warning", -"5 - notification", -"6 - informational", -"7 - debugging" | table host "0 - emergency" "1 - alert" "2 - critical" "3 - error" "4 - warning" "5 - notification" "6 - informational" "7 - debugging"
Hope to have explaned clearly.
thanks
UPDATE
i'm going to this about this filter could be applied only to PIVOT queries..
because working a little bit more on the previous posted PIVOT query i had successful results.
But e.g. on the following NON-PIVOT query i'm still have issues:
eventtype=cisco_ios-duplex_mismatch | dedup dvc,cdp_local_interface | table _time,dvc,cdp_local_interface,cdp_neighbor,dest_interface,message_text | rename cdp_local_interface AS "Local Int.",cdp_neighbor AS "CDP Neighbor",dest_interface AS "Remote Int.",message_text AS "Message" | sort dvc
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@null0, what is the definition of your eventtype eventtype=cisco_ios-duplex_mismatch? What is the host fieldname for cisco_ios-duplex_mismatch ? Is it host?
have you tried a filter like the following in your base search with eventtype (where host field name in your raw data is host)?
eventtype=cisco_ios-duplex_mismatch host="$host$"
| dedup dvc,cdp_local_interface
| table _time,dvc,cdp_local_interface,cdp_neighbor,dest_interface,message_text
| rename cdp_local_interface AS "Local Int.",cdp_neighbor AS "CDP Neighbor",dest_interface AS "Remote Int.",message_text AS "Message"
| sort dvc
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@null0, what is the definition of your eventtype eventtype=cisco_ios-duplex_mismatch? What is the host fieldname for cisco_ios-duplex_mismatch ? Is it host?
have you tried a filter like the following in your base search with eventtype (where host field name in your raw data is host)?
eventtype=cisco_ios-duplex_mismatch host="$host$"
| dedup dvc,cdp_local_interface
| table _time,dvc,cdp_local_interface,cdp_neighbor,dest_interface,message_text
| rename cdp_local_interface AS "Local Int.",cdp_neighbor AS "CDP Neighbor",dest_interface AS "Remote Int.",message_text AS "Message"
| sort dvc
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
well it seems working fine adding host="$host$" to NON_PIVOT query you posted. I'll try soon to adapt all others queries and will send you a feedback.
thanks a lot
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sure, check and revert back. If your issue gets resolved, don't forget to accept the answer 🙂
| makeresults | eval message= "Happy Splunking!!!"