- Splunk Answers
- :
- Splunk Administration
- :
- Deployment Architecture
- :
- Re: I edited inputs.conf on deployment client to m...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I edited inputs.conf on deployment client to monitor path that has all the symantec logs in one directory through syslog. Please help me how to get separate sourcetypes ??
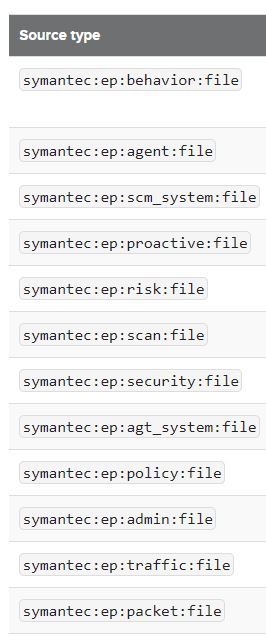
I need to get the following sourcetypes? i have all the symantec logs dumped into single directory by external logging option enabled in SEPM
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Symantec TA wants you to configure your inputs like this (according to the included inputs.conf.template):
[monitor://<<path_to_temp_dump_file_directory>>/scm_admin.tmp]
sourcetype = symantec:ep:admin:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_behavior.tmp]
sourcetype = symantec:ep:behavior:file
[monitor://<<path_to_temp_dump_file_directory>>/scm_agent_act.tmp]
sourcetype = symantec:ep:agent:file
[monitor://<<path_to_temp_dump_file_directory>>/scm_policy.tmp]
sourcetype = symantec:ep:policy:file
[monitor://<<path_to_temp_dump_file_directory>>/scm_system.tmp]
sourcetype = symantec:ep:scm_system:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_packet.tmp]
sourcetype = symantec:ep:packet:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_proactive.tmp]
sourcetype = symantec:ep:proactive:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_risk.tmp]
sourcetype = symantec:ep:risk:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_scan.tmp]
sourcetype = symantec:ep:scan:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_security.tmp]
sourcetype = symantec:ep:security:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_system.tmp]
sourcetype = symantec:ep:agt_system:file
[monitor://<<path_to_temp_dump_file_directory>>/agt_traffic.tmp]
sourcetype = symantec:ep:traffic:file
You said all the log files are in one location, but you didn't say all the different types were in the same file, so I think the above should still be feasible for you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Are those different files or every data is dumped into single file on your syslog server?
If it is different files, then you can configure inputs.conf and props.conf something like this
In below example we are configuring universal forwarder to monitor /var/tmp/abc.log and /var/tmp/xyz.log
inputs.conf
[monitor:///var/tmp/]
whitelist = (abc|xyz)\.log
index=test
props.conf
[source::/var/tmp/abc.log]
sourcetype = symantec:ep:risk:file
[source::/var/tmp/xyz.log]
sourcetype = symantec:ep:scan:file
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@harsmarvania57
It is every data dumped into single file on my syslog server.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok, then it will be tricky to assign different sourcetype. You can use props.conf and transforms.conf on indexer/forwarder to change sourcetype based on regex.
Here are example (In below example I have provided <yourregex> in transforms.conf in which you need to write regular expression to find different data and based on that splunk will assign that sourcetype):
props.conf
[yoursourcetypefromUF]
TRANSFORMS-sourcetype = override-sourcetype, override-sourcetype-1
transforms.conf
[override-sourcetype]
DEST_KEY = MetaData:Sourcetype
REGEX = <yourregex>
FORMAT = symantec:ep:risk:file
[override-sourcetype-1]
DEST_KEY = MetaData:Sourcetype
REGEX = <yourregex>
FORMAT = symantec:ep:scan:file
I would recommend to dump different type of data in different files on syslog server if possible which is easiest way to achieve your requirement.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@harsmarvania57
Can i dump it to different files at syslog level if so how do i it?
This is my email sridharclear@gmail.com
can you ping me on it? can you guide me please?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I am not symantec and syslog expert so I can't help on this, maybe you need to take help from your organizations who generally configure syslog server.