Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Re: Tokens flicking to $TOKEN$ and back to value w...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
HI
I am displaying a token that is refreshing every 10 seconds - but now that I have added a base search the token is flicking to $result.TIME$ on the screen and then back to the value.
How do I use a base search and not have the token flick?
I have put both examples below one working(not base search) and one not working.
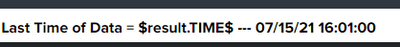
I have tried to change finalized to done - but nothing changed. We can see in the image one working and one displaying the token (only for 1 second until the search is finished, but it doe not look nice)
<search base="basesearch_MAIN">
<!-- Displays the last time pack that has entered SPLUNK - THis need to be update to use the base search off the main search -->
<query>| rename _time as TIME | eval TIME=strftime(TIME,"%m/%d/%y %H:%M:%S")
| table TIME | tail 1</query>
<finalized>
<set token="Token_TIME_OF_LAST_DATA">$result.TIME$</set>
<finalized>
</search>
NO BASE SEARCH - This does not jump on the screen
<search>
<query>| mstats max("mx.process.cpu.utilization") as cpuPerc WHERE "index"="metrics_test" AND mx.env=MONITORING_MVP span=10s | rename _time as TIME | eval TIME=strftime(TIME,"%m/%d/%y %H:%M:%S")
| table TIME | tail 1</query>
<earliest>-1m</earliest>
<latest>now</latest>
<finalized>
<set token="Token_TIME_OF_LAST_DATA1">$result.TIME$</set>
</finalized>
<refresh>10s</refresh>
</search>
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try
<progress>
<condition match=" $job.resultCount$ == 1">
<set token="Token_TIME_OF_LAST_DATA1">$result.TIME$</set>
</condition>
</progress>- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi - Thanks for the answer.
I did not try your answer as I was able to go with the accepted solution above.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try
<progress>
<condition match=" $job.resultCount$ == 1">
<set token="Token_TIME_OF_LAST_DATA1">$result.TIME$</set>
</condition>
</progress>- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Wonderfull thanks - 🙂 It works for a TIME token - cheers
Also below is another example of how to do it
<search base="basesearch_MAIN">
<!-- FInd out how many process are being monitored -->
<query>| stats count </query>
<progress>
<condition match=" $result.count$ != 0">
<set token="Token_no_of_Process">$result.count$</set>
</condition>
</progress>
</search>
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm not sure whether it is possible to manage token in xml like your requirement with base search. But I have done it with use of JS. May be if you want to check it.
<dashboard script="a.js">
<label>Sample Dashboard</label>
<search id="base_search">
<query>| makeresults count=1000000 </query>
<refresh>10s</refresh>
<earliest>-24h@h</earliest>
<latest>now</latest>
</search>
<row>
<panel>
<title>$Token_TIME_OF_LAST_DATA$</title>
<table>
<search id="child_id" base="base_search">
<query>| rename _time as TIME | eval TIME=strftime(TIME,"%m/%d/%y %H:%M:%S") | table TIME | head 1</query>
</search>
<option name="drilldown">none</option>
</table>
</panel>
</row>
</dashboard>
a.js
require([
'underscore',
'jquery',
'splunkjs/mvc',
'splunkjs/mvc/simplexml/ready!'
], function(_, $, mvc) {
var mySearch = mvc.Components.get('child_id');
var tokens = mvc.Components.get("default");
tokens.set("Token_TIME_OF_LAST_DATA", " ");
mySearch.on('search:done', function(properties) {
var myResults = mySearch.data("results"); // get the data from that search
myResults.on("data", function() {
resultArray = myResults.data().rows;
tokens.set("Token_TIME_OF_LAST_DATA", resultArray[0]);
})
});
});
Thanks
KV
▄︻̷̿┻̿═━一
If any of my reply helps you to solve the problem Or gain knowledge, an upvote would be appreciated.