Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Dashboards & Visualizations
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Re: Query with multiple values in cell
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Query with multiple values in cell
rangarbus
Path Finder
03-10-2021
09:00 AM
Hey friends, I am facing a problem with my new dashboard.
My Event:
{
kubernetes: {
container_name: adapter
docker_id: a15db0337d70979f0f6e042f5bd609bfe1c42a97472faea56c77924c2ec43158
namespace_name: default
pod_name: adapter-767585d989-x5fj7
}
log: {"thread":"simpleMessageListenerContainer-2","level":"INFO","loggerName":"adapter.repository.S3Repository","message":"Getting s3object bucket=adapter-test, key=in/1234.json","endOfBatch":true,"loggerFqcn":"org.apache.logging.slf4j.Log4jLogger","instant":{"epochSecond":1615350586,"nanoOfSecond":904000000},"threadId":14,"threadPriority":5,"app_name":"adapter"}
log_processed: {
app_name: adapter
endOfBatch: true
instant: {
epochSecond: 1615350586
nanoOfSecond: 904000000
}
level: INFO
loggerFqcn: org.apache.logging.slf4j.Log4jLogger
loggerName: adapter.repository.S3Repository
message: Getting s3object bucket=adapter-test, key=in/1234.json
thread: simpleMessageListenerContainer-2
threadId: 14
threadPriority: 5
}
stream: stdout
time: 2021-03-10T04:29:46.90639262Z
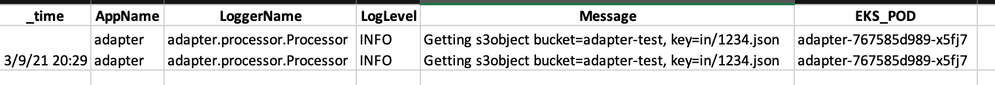
}When i create a dashboard out of this event, I get 2 entries on each cell of the dashboard.
My dashboard query is as below
index=logs sourcetype=test
| rename log_processed.app_name as AppName
| rename log_processed.loggerName as LoggerName
| rename log_processed.level as LogLevel
| rename log_processed.message as Message
| rename kubernetes.pod_name as EKS_POD
| table _time, AppName, LoggerName, LogLevel, Message, EKS_POD
| where Message!=""Output is like:
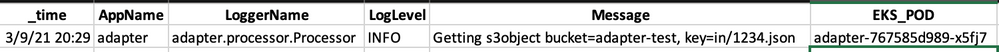
Ideally the output should be :
Could you please help on this.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ITWhisperer

SplunkTrust
03-10-2021
03:02 PM
| foreach * [ eval <<FIELD>>=mvdedup('<<FIELD>>') ]- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
03-10-2021
02:01 PM
Does the props.conf file contain both KV_MODE=JSON and AUTO_KV_JSON=true? If so, that's why the fields are doubled.
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Get Updates on the Splunk Community!
New Year, New Changes for Splunk Certifications
As we embrace a new year, we’re making a small but important update to the Splunk Certification ...
[Puzzles] Solve, Learn, Repeat: Unmerging HTML Tables
[Puzzles] Solve, Learn, Repeat: Unmerging HTML TablesFor a previous puzzle, I needed some sample data, and ...
Enterprise Security (ES) Essentials 8.3 is Now GA — Smarter Detections, Faster ...
As of today, Enterprise Security (ES) Essentials 8.3 is now generally available, helping SOC teams simplify ...