Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- Re: TA-SymantecWebSecurityService not working prop...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
WSS input is unresponsive.
A) getting socket errors when connnecting to localhost scwss-poll
B) submitting input XML form with input name/credentials to API - not working - throwing error from splunkd as unresponsive.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
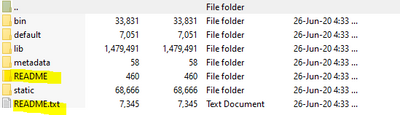
in the 2.0.0 version of the TA there is a Readme folder that explains the input.conf stanza.
also keep in mind you need to hardcode the index in inputs.conf
in the README folder the inputs.conf.spec shows all parameters that can be configured in inputs.conf
[scwss-poll://<name>]
apiusername = <value>
*Cloud-driven Web Security Service API Username
apikey = <value>
*Cloud-driven Web Security Service API Key
start_time = <value>
*Data-collection start-time
* HTTPS proxy server address
https_proxy = <value>
* HTTPS proxy server port
https_proxy_port = <value>
* HTTPS proxy server username
https_proxy_username = <value>
* HTTPS proxy server password
https_proxy_password = <value>
python.version = <value>
the default or LOCAL inputs.conf contains:
***** please note index needs hardcoded in inputs.conf as index="wss" or logs end up in main****
[scwss-poll]
interval = 3600
sourcetype = symantec:websecurityservice:scwss-poll
python.version = python3
[batch://$SPLUNK_HOME/var/spool/splunk/...stash_ta_scwss_logs.zip]
index=wss
sourcetype = symantec:websecurityservice:scwss-poll
move_policy = sinkhole
[batch://$SPLUNK_HOME\var\spool\splunk\...stash_ta_scwss_logs.zip]
sourcetype = symantec:websecurityservice:scwss-poll
move_policy = sinkhole
So what would a Complete stanza look like?
i.e. hardcoded to /TA-SymantecWebSecurityService/default/inputs.conf
[scwss-poll://<name>]
interval = 3600
sourcetype = symantec:websecurityservice:scwss-poll
python.version = python3
apiusername = <value>
*Cloud-driven Web Security Service API Username
apikey = <value>
*Cloud-driven Web Security Service API Key
start_time = <value>
*Data-collection start-time
* HTTPS proxy server address
https_proxy = <value>
* HTTPS proxy server port
https_proxy_port = <value>
* HTTPS proxy server username
https_proxy_username = <value>
* HTTPS proxy server password
https_proxy_password = <value>
[batch://$SPLUNK_HOME/var/spool/splunk/...stash_ta_scwss_logs.zip]
index=wss
sourcetype = symantec:websecurityservice:scwss-poll
move_policy = sinkhole
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
for problem A) the app is looking for admin user so in a cloud environment make sure to ask support to validate permissions.
i.e. allow sc_admin to write to the app.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
on an additional note,
modifying in $SPLUNKDIR/etc/apps/TA-SymantecWebSecurityService/bin
logger_manager.py
logfile = make_splunkhome_path(["var", "log", "scwss",
"%s.log" % log_name])
logdir = os.path.dirname(logfile)
to splunk will allow you to ingest the scwss-poll.log generated by the scwss-poll.py script in _internal
as the current set up may fail to pull the log file unless you add a new file monitor on the scwss dir.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
in the 2.0.0 version of the TA there is a Readme folder that explains the input.conf stanza.
also keep in mind you need to hardcode the index in inputs.conf
in the README folder the inputs.conf.spec shows all parameters that can be configured in inputs.conf
[scwss-poll://<name>]
apiusername = <value>
*Cloud-driven Web Security Service API Username
apikey = <value>
*Cloud-driven Web Security Service API Key
start_time = <value>
*Data-collection start-time
* HTTPS proxy server address
https_proxy = <value>
* HTTPS proxy server port
https_proxy_port = <value>
* HTTPS proxy server username
https_proxy_username = <value>
* HTTPS proxy server password
https_proxy_password = <value>
python.version = <value>
the default or LOCAL inputs.conf contains:
***** please note index needs hardcoded in inputs.conf as index="wss" or logs end up in main****
[scwss-poll]
interval = 3600
sourcetype = symantec:websecurityservice:scwss-poll
python.version = python3
[batch://$SPLUNK_HOME/var/spool/splunk/...stash_ta_scwss_logs.zip]
index=wss
sourcetype = symantec:websecurityservice:scwss-poll
move_policy = sinkhole
[batch://$SPLUNK_HOME\var\spool\splunk\...stash_ta_scwss_logs.zip]
sourcetype = symantec:websecurityservice:scwss-poll
move_policy = sinkhole
So what would a Complete stanza look like?
i.e. hardcoded to /TA-SymantecWebSecurityService/default/inputs.conf
[scwss-poll://<name>]
interval = 3600
sourcetype = symantec:websecurityservice:scwss-poll
python.version = python3
apiusername = <value>
*Cloud-driven Web Security Service API Username
apikey = <value>
*Cloud-driven Web Security Service API Key
start_time = <value>
*Data-collection start-time
* HTTPS proxy server address
https_proxy = <value>
* HTTPS proxy server port
https_proxy_port = <value>
* HTTPS proxy server username
https_proxy_username = <value>
* HTTPS proxy server password
https_proxy_password = <value>
[batch://$SPLUNK_HOME/var/spool/splunk/...stash_ta_scwss_logs.zip]
index=wss
sourcetype = symantec:websecurityservice:scwss-poll
move_policy = sinkhole