Join the Conversation
- Find Answers
- :
- Apps & Add-ons
- :
- All Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Lookup command doesn't support dot notation in fie...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lookup command doesn't support dot notation in field name
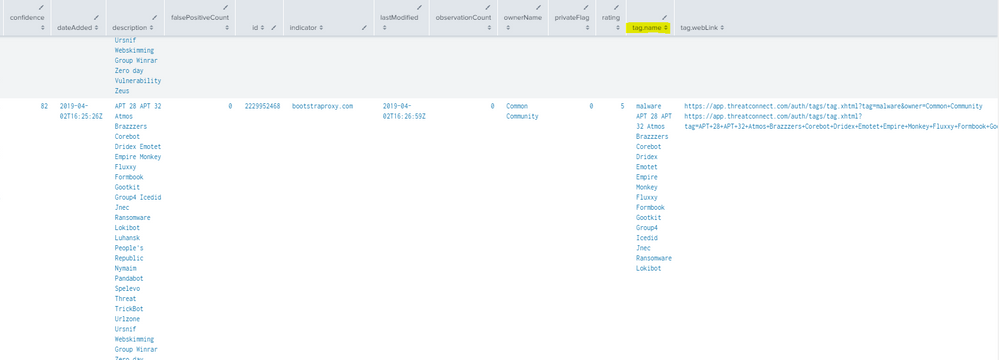
Hi, I'm working with Threatconnect lookup created by their add on, one of the kvstores has one field within a collection, the field name in the kvstore definition is tag, that field has multiple values for tag.name.
For example, one row will be like the following:
webLink: https://app.threatconnet.com
rating: 5.0
confidence: 80
indicator: 101.1.8.1
tag.name: malware
.name: Corebot
.name: Ransomware
The field tag is part of the supported fields, however, I'm not able to make searches over that field using lookup command
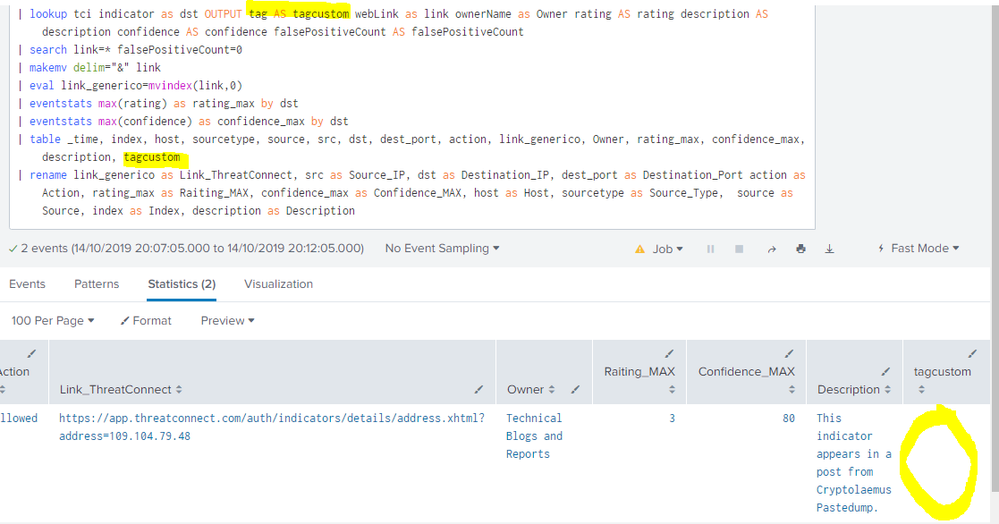
If I use |lookup tci indicator as dest OUTPUT tag as tagcustom | table dest, tag the tag column is empty.
If I use |lookup tci indicator as dest OUTPUT tag.name as tagcustom | table dest, tagcustom I get an splunk error "Error in 'lookup' command: Could not find all of the specified destination fields in the lookup table."
I would like to use search command to find custom tag.name but it doesn't work.
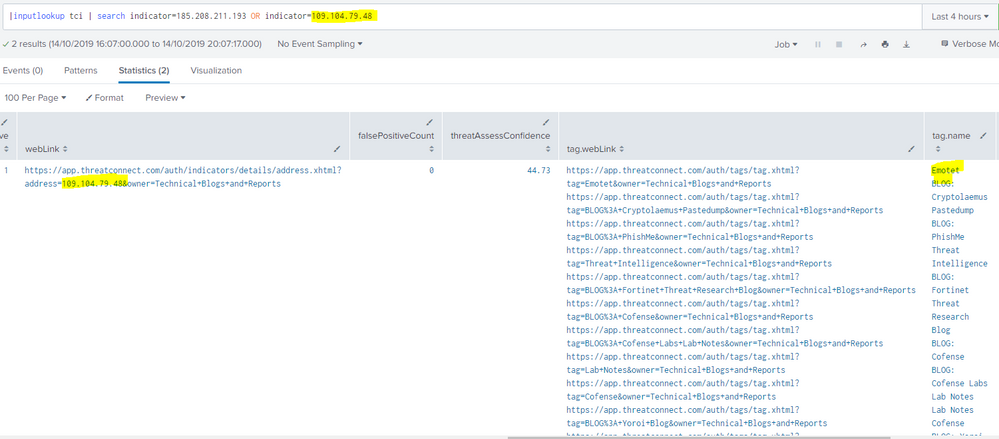
Notice that the tag field has values because when I use the command
|inputlookup tci |search tag.name=Corebot I get information in that column.
I would like to know if there is possible to use lookup command to retrieve tag.name. I know that I can use a subsearch with the inputlookup command, but I think it is not efficient.
Thanks in advance for your help.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm also facing the same issue, while using threatconnect app fields tag.name & tag.weblink in lookup command output.
Actually, splunk supports dot notation on the normal lookups, i won't face issue on it. But on the threatconnect app, tag field is consist of name & weblink [key-value pairs]. While trying to access tag.name & tag.weblink in lookup command facing issue.
Can anyone help on this.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
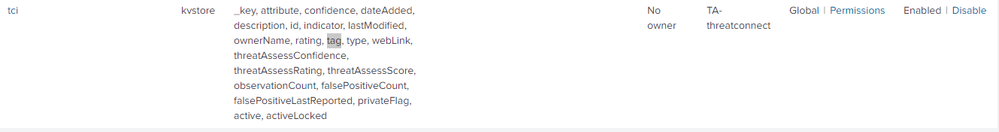
Thanks for your answers, I just want to let you know the definition of the kvstore is the following:
They just define tag, but I know that inside tag there is the name. However, when I use tag.name, I get "Error in 'lookup' command: Could not find all of the specified destination fields in the lookup table."
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This has NOTHING to do with it. Did you look at my answer and the clarifying comment? Your SPL is backwards.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are swapping arguments and putting them in the wrong place. Here is a run anywhere example that works (it has nothing to do with the dot):
| makeresults
| eval tag.name="microsoft.com"
| lookup dnslookup clienthost AS tag.name OUTPUT clientip AS tag.name2
You have your field names in the OUTPUT swapped so you get an error like this:
| makeresults
| eval tag.name="microsoft.com"
| lookup dnslookup clienthost AS tag.name OUTPUT tag.name2 AS clientip
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In other words, do this:
... | lookup tci indicator ASdest OUTPUT tag AS tag.name | table dest, tag
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I did a test in my personal splunk and it had worked get data from fields like "tag.name". May you have to revist your code to get it done properly.
I created a csv file with 2 fiels, cod and tag.name and added fake data to match my VendorID code.
Here is the command I used to search the respective VendID code at lookup table and output tag.name. I used a stat before apply the lookup command.
index=main VendorID=* | stats count by VendorID | lookup lktest cod as VendorID Output tag.name | sort by tag.name
https://docs.splunk.com/Documentation/Splunk/7.3.2/SearchReference/Lookup!
alt text