Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Alerting
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- Machine Learning Outliers in Enterprise Security
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Machine Learning Outliers in Enterprise Security
daniel_althoff8
Loves-to-Learn
07-29-2021
06:27 AM
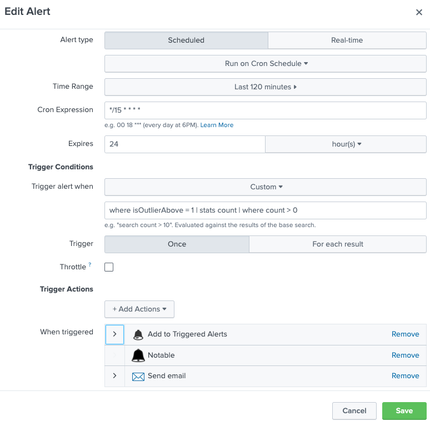
I have set up some Numerical Outlier detections in the MLTK, on our ES Search Head.
They are set up as alerts in Splunk on our Enterprise Security Search Head.
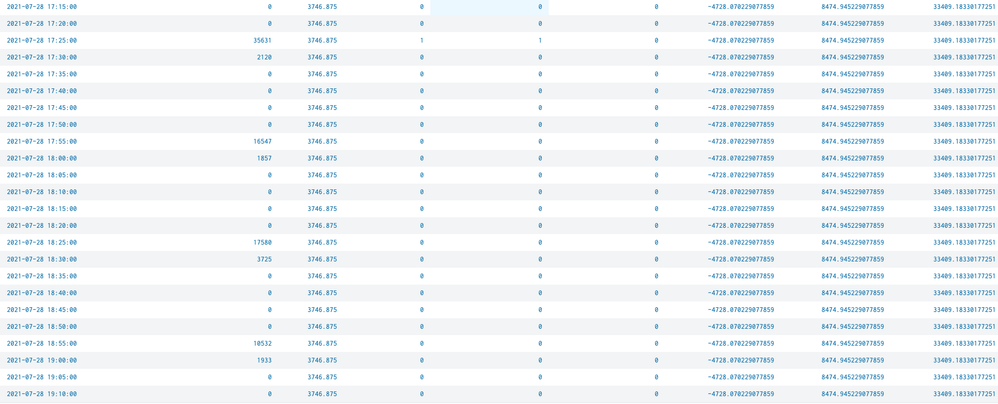
The Numerical Outlier alert looks back over a 2 hour time range. Which creates 24 data points (120 mins / 5 min increments = 24 event data points)
The problem is - in Enterprise Security (since this is a notable event), we receive 24 separate notable events! We correctly only receive 1 email each time the alert fires, but 24 notable events in ES.
I have the alert set to trigger "Once", rather than "Per Result"
Is there anything else I can do to make sure ES doesn't get slammed with 24 notables every time this alert fires?
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
SOK it to Me: Top 3 Benefits of Using Splunk Operator on Kubernetes that’ll Make ...
Thursday, July 9, 2026 | 11:00AM–12:00PM PDT
Duration: 1 hour (includes Q&A)
Managing can feel like a ...
Upgrade Prep for 10.4, Network Observability Deep Dives, and More from Splunk Lantern
Splunk Lantern is Splunk’s customer success center that provides practical guidance from Splunk experts on key ...
Splunk Developer Day announcements: AI agents, MCP tools, Forecasting, and Custom ...
Splunk Developer Day was packed with product and platform updates for developers building in the AI ...