Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- How to write a search to alert when a source stops...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to write a search to alert when a source stops sending Windows event log data?
Hello,
Need a suggestion to set up an alert for when a source stops sending Windows event data. Here is what I have so far, but is this sufficient?
index=windows host=#1 OR host=#2 OR host=#3 | stats count by host | where count<1
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I had to set up a negative alert the other day just like this.. It's very simple to do
Put in your search which will return results
index=windows host=#1 OR host=#2 OR host=#3
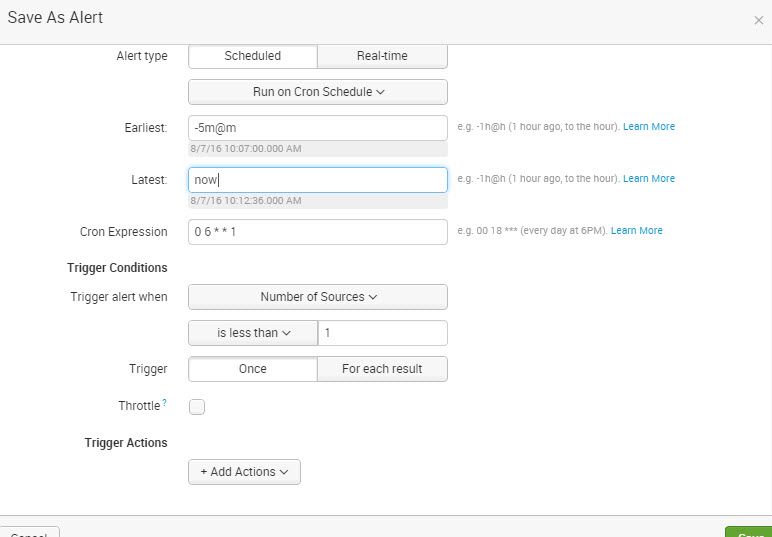
Then save as alert then go to where it says Trigger alert when then change to Number of sources and is less than then select your time frame.. In the image I selected 5 minutes.. So this will say, send an alert anytime there is less than 1 new source in a 5 minute window, and the search will run every 5 minutes.. So if your not getting atleast 1 new source every 5 minutes then the alert will fire
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
for this task, i hope using metadata would be efficient.
This one will find the hosts that have not sent any events for more than one day.
| metadata type=hosts index=windows host=one (or .....)| where relative_time(now(), "-1d") > lastTime | convert ctime(lastTime) as Latest_Time | sort -lastTime | table host,Latest_Time
A general query
| metadata type=hosts | sort recentTime desc | convert ctime(recentTime) as Recent_Time
Sekar
PS - If this or any post helped you in any way, pls consider upvoting, thanks for reading !