Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Other Using Splunk
- :
- Alerting
- :
- Re: Alert not triggering
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I'm trying to receive an alert if any of my hosts stop sending events for a period of time.
The query | metadata type=hosts | eval age=(recentTime-now()) | where age<-1 | table host recentTime age | convert ctime(recentTime) shows a number of results.
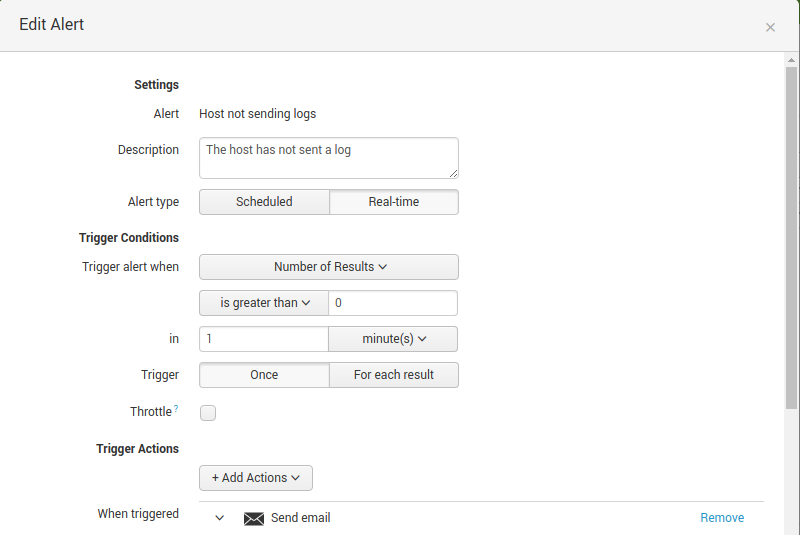
I am creating a real-time alert from this query and setting it to trigger when the number of results is greater than 0.
The alert is not being triggered, even though the search query that it is built from is returning results.
Obviously when I have worked it out I will increase the number of seconds that I compare "age" against, but now I can't work out why the alert is not being triggered.
Thanks,
Andy
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Could you please read the answer provided in our community
https://answers.splunk.com/answers/509671/why-is-my-simple-alert-not-firing.html
https://answers.splunk.com/answers/223399/why-is-my-simple-alert-not-being-triggered-with-th.html
Hope it will help you
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Could you please read the answer provided in our community
https://answers.splunk.com/answers/509671/why-is-my-simple-alert-not-firing.html
https://answers.splunk.com/answers/223399/why-is-my-simple-alert-not-being-triggered-with-th.html
Hope it will help you
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reply, but I'm not sure how to apply those answers. My search is real-time and so is my alert. I've also tried a rolling window for search and a scheduled alert.