- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to seperate succefully login attempt from invl...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
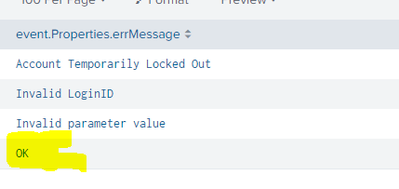
How to seperate succefully login attempt from invlaid Login id
Hi Team
Can anyone help me with Splunk search query to split the successful login from invalid?
Ex - I want to exclude OK from the search, want to see only the locket out, invalid, invalid parameter
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tried,, but the search returning no result.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Whenever you use a field name in an 'eval' expression (where requires an eval expression), you need to use single quotes around the field name if the field name is on the right hand side of the eval statement and contains non-simple characters (in this case the full stop), so
| where 'event.Properties.errMessage' != "OK"Note the sometimes confusing use of single and double quotes used, for example this statement
| eval event.Properties.errMessage="Hello"does NOT need quotes on the left hand side of the statement.
Where necessary, the left hand side use of quotes requires double quotes, so if your field name has a space, you would need
| eval "My Field With Spaces"="Hello"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Or based on your other question, you can directly set that criteria in the initial search, i.e.
index=test event.Properties.errMessage!=OK- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| where event.Properties.errMessage != "OK"- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
How do i seperate multiple error instead " OK "
Invalid password, reset password, permission denied etc
index=events event.Properties.errMessage != "Invalid LoginID","Account Temporarily Locked Out","Permission denied""Unauthorized user","Account Pending Verification","Invalid parameter value"
| stats count by event.Properties.errMessage
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
index=events event.Properties.errMessage!="Invalid LoginID" event.Properties.errMessage!="Account Temporarily Locked Out" event.Properties.errMessage!="Permission denied" event.Properties.errMessage!="Unauthorized user" event.Properties.errMessage!="Account Pending Verification" event.Properties.errMessage!="Invalid parameter value"
| stats count by event.Properties.errMessage