Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- tstats behaviour change in Splunk 6.6, expected ch...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi !
Splunk 6.6 being out officially, I had the (bad) surprise to discover is very annoying change in tstats command behaviour.
Doing an operation over a non existing field result in a "nan" value instead of a null field.
The following search can be used to demonstrate:
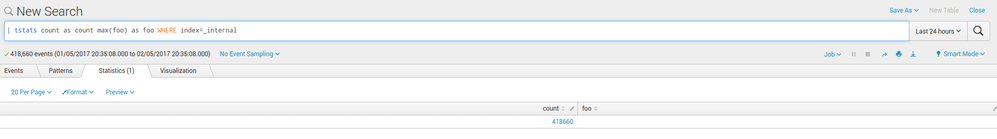
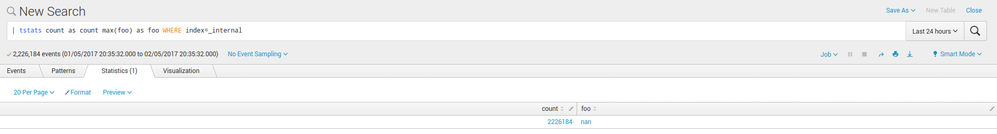
| tstats count as count max(foo) as foo WHERE index=_internal
With 6.5.3 and previous, the result would have been:
Since 6.6, it is now:
So in what could be a problem ? Well it changes the behaviour on any condition using an "isnull" or "isnotnull" condition, such as:
| tstats count as count max(foo) as foo WHERE index=_internal
| eval good=if(isnotnull(foo), foo, count)
Would now use the "bad" value instead of the "good" value, because it is not null any more as it now equals to the "nan" string.
Off course, the query can be changed to something like:
| tstats count as count max(foo) as foo WHERE index=_internal
| eval good=if(isnum(foo), foo, count)
This is however a serious change in the tstats behaviours, and has side effects on any stuff doing such job and assuming that the field will be null if it is not available in the data.
Is that an expected change ? A bug ?
Thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This issue has been fixed with Splunk maintenance release 6.6.1 (SPL-141863, SPL-141584)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This issue has been fixed with Splunk maintenance release 6.6.1 (SPL-141863, SPL-141584)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Happy to have that one in my Jira scrapbook! 😉
Thanks for finding it early and reporting @guilmxm

- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And more than happy to contribute to the quality of Splunk 😉
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you referring to 6.6.1 ? Not 6.1.1?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
A typo off course, thank you 😉
Corrected.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks as always for your rockstar work, Guilhem!
I have filed a bug and made internal devs aware. Stay tuned!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm going with bug. I've seen nans before and it wa always my fault and not expected 😉