Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- how to rename column name based on condition
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
how to rename column name based on condition
hqw
Path Finder
10-28-2015
09:47 PM
Hi all,
I want to name the column name based on condition as below snapshot, for example, if Q1=A, then rename row 1 as text1, if Q2 is B then rename row is text 2.
Do you guys know how to achieve this?
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
akanno
Communicator
10-29-2015
01:19 AM
Do you use the transpose command like following?
index=_internal | stats count by sourcetype | transpose 7
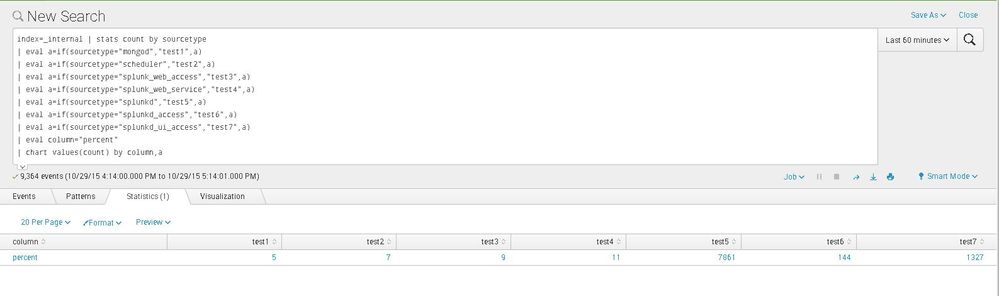
you can use eval command and chart command instead of using the transpose command
try this search
index=_internal | stats count by sourcetype
| eval a=if(sourcetype="mongod","test1",a)
| eval a=if(sourcetype="scheduler","test2",a)
| eval a=if(sourcetype="splunk_web_access","test3",a)
| eval a=if(sourcetype="splunk_web_service","test4",a)
| eval a=if(sourcetype="splunkd","test5",a)
| eval a=if(sourcetype="splunkd_access","test6",a)
| eval a=if(sourcetype="splunkd_ui_access","test7",a)
| eval column="percent"
| chart values(count) by column,a
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hqw
Path Finder
10-28-2015
10:45 PM
sorry if Q0=A, then column name = text1, if Q0= B then column name = text2. Since I have sort the Q0, so the order of A B C D E would be change automatically, that is why I need use Q0 as a condition to rename column name.
Get Updates on the Splunk Community!
Splunk Observability Cloud's AI Assistant in Action Series: Auditing Compliance and ...
This is the third post in the Splunk Observability Cloud’s AI Assistant in Action series that digs into how to ...
Splunk Community Badges!
Hey everyone! Ready to earn some serious bragging rights in the community? Along with our existing badges ...
What You Read The Most: Splunk Lantern’s Most Popular Articles!
Splunk Lantern is a Splunk customer success center that provides advice from Splunk experts on valuable data ...