Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- compare find missing values from two indexes same...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
compare find missing values from two indexes same field heading /name
learningnow
New Member
09-30-2019
09:37 AM
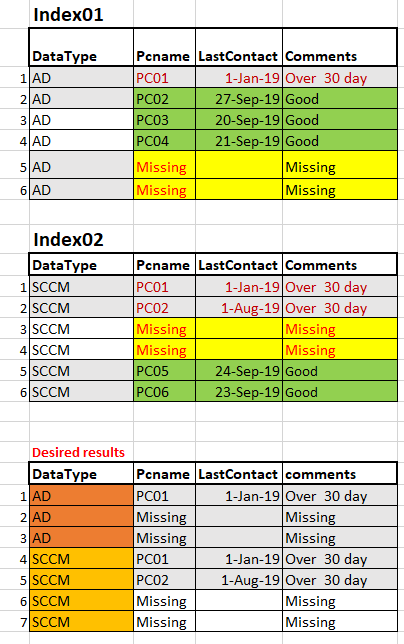
Trying to create a report using two indexes on same field "Pcname".
Different datatype one of from Active Directory and other one is from SCCM.
Same computer are present in both indexes
see also the attach screen short.
Desire results:
- If missing form for either Index or not reported back in last 30 days
- nice it have one report but if not possible then we can break in 2 reports or more if needed
Thanks in advance
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jkat54

SplunkTrust
09-30-2019
12:30 PM
Something like this:
index=ad OR index=sccm
| eval pcName=coalesc(pcname_field_in_AD_index, pcname_field_in_SCCM_index)
| eval lastContact=coaslesc(lastContact_field_in_AD_index, lastContact_field_in_SCCM_index)
| fillnull value="missing"
| stats latest(lastContact) as lastContact by pcName index
| eval comments="Logic for missing / over 30 days goes here"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
learningnow
New Member
09-30-2019
01:15 PM
Thanks let me try if this would work
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Build the Future of Agentic AI: Join the Splunk Agentic Ops Hackathon
AI is changing how teams investigate incidents, detect threats, automate workflows, and build intelligent ...
[Puzzles] Solve, Learn, Repeat: Character substitutions with Regular Expressions
This challenge was first posted on Slack #puzzles channelFor BORE at .conf23, we had a puzzle question which ...
Splunk Community Badges!
Hey everyone! Ready to earn some serious bragging rights in the community? Along with our existing badges ...