Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Why do I not get the same results for (search stat...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
I try Splunk myself after I've join in Splunk beginning Course and found this strange result. Is it bug or something?
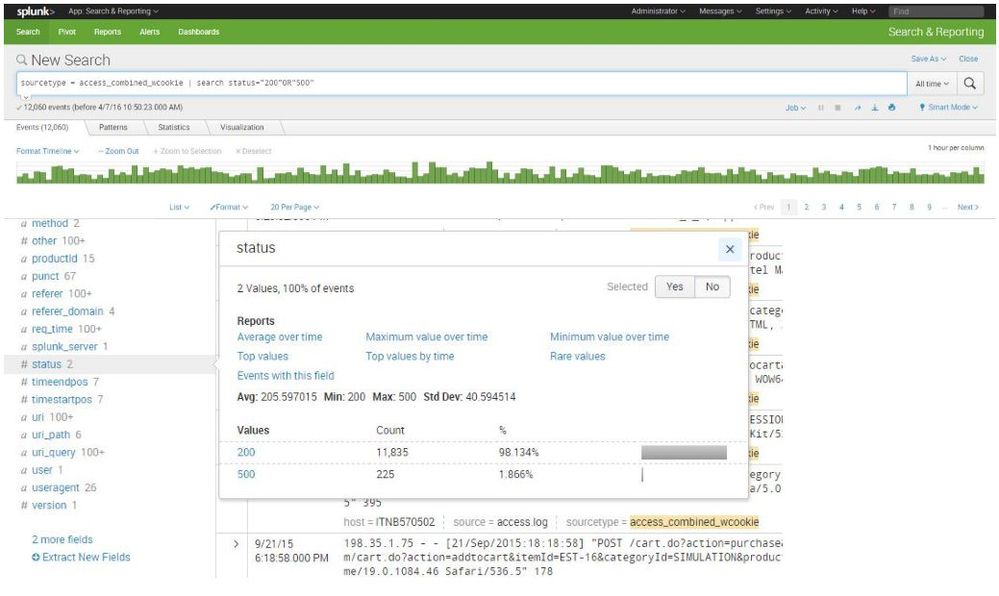
sourcetype = access_combined_wcookie | search status="200"OR"500"
is not same as
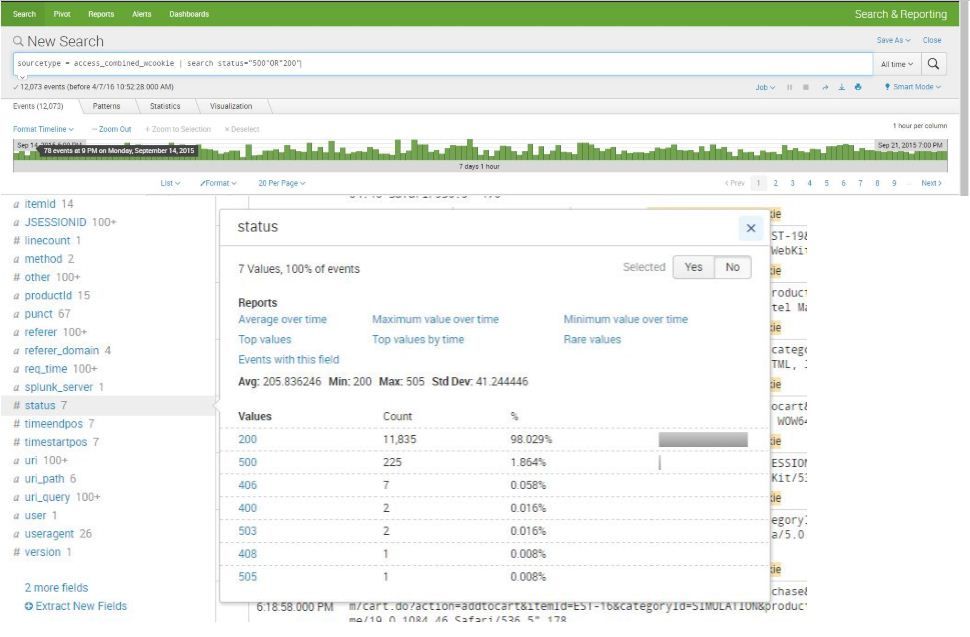
sourcetype = access_combined_wcookie | search status="500"OR"200"
Splunk Source is website access.log and status is access status log.
Why?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
status="200"OR"500" means "status equals 200 OR raw event contains 500"
status="500"OR"200" means "status equals 500 OR raw event contains 200"
These do not mean "status equals 200 OR status equals 500"!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
status="200"OR"500" means "status equals 200 OR raw event contains 500"
status="500"OR"200" means "status equals 500 OR raw event contains 200"
These do not mean "status equals 200 OR status equals 500"!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Exactly. Implicitly, your old search was parenthesized as ( ( status="200" ) OR ( "500" ) ).
While you're at it, do not write searches like sourcetype=foo | search field=value, instead use sourcetype=foo field=value directly. Otherwise, Splunk would load all data from that sourcetype and then filter instead of only loading data matching both filters - such performance, much fast, wow.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you very much
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So
In order to find status 200 or 500
It has to command like
search status="500"OR status="200"
or
search status="200"OR status="500"
right?
I have try it
and result shown it equal now
Thank you !!!