Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Top & Fields command
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Top & Fields command
anasshsa
Engager
04-16-2019
02:00 AM
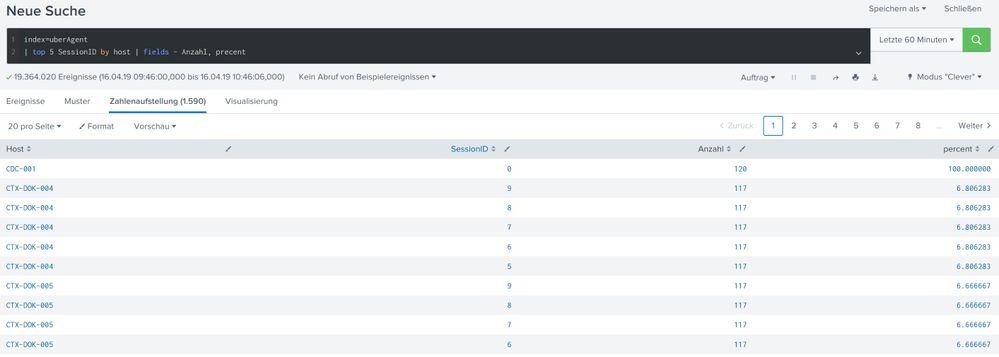
index=uberAgent
| top 5 SessionID by host | fields - Anzahl, precent
This code returns all events in the index instead of five and removes no counts and percent fields. Who can be the problem?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
somesoni2
Revered Legend
04-16-2019
07:41 AM
Your query is fetching top 5 sessionID for each host (all hosts will be shown). What was your requirement?
Regarding removing the fields, the percent field name is misspelled (written as precent) hence it's not removed. For removing count, try to use field name count itself. (try | fields - count, percent)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
niketn
Legend
04-16-2019
09:17 AM
@somesoni2 actually better would be to use showperc=f and showcount=f arguments in the top command itself.
| top 5 SessionID by host showperc=f showcount=f
@anasshsa your query id giving you top 5 sessions for each host. If that is your requirement you can try the following:
index=uberAgent
| top 5 SessionID by host showperc=f
| xyseries host SessionID count
Please let us know if you are looking for something else.
____________________________________________
| makeresults | eval message= "Happy Splunking!!!"
| makeresults | eval message= "Happy Splunking!!!"
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Mile High Learning with Splunk University, Denver, Colorado
If Denver is known for its mile-high elevation, Splunk University is about to raise the bar on technical ...
IT Service Intelligence 5.0 Series: Your Guide to the June Launch
We are excited to announce the June release of Splunk IT Service Intelligence (ITSI) 5.0. This update ...
Agent Mode Engaged! Enchaining Agentic Operations with Splunk AI Assistant 2.0
Are you ready to transform how your team handles complex data requests?
We invite you to our upcoming ...