Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- To extract a field using the REX Command
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello
I want to extract the field issrDsclsrReqId" using the Rex command.
Can someone please help me with the command to extract the value of field bizMsgIdr which is eiifr000005229220231229162227.
{ "shrhldrsIdDsclsrRspn": { "dsclsrRspnId": "0000537ede1c5e1084490000aa7eefab", "issrDsclsrReqRef": { "issrDsclsrReqId": "eiifr000005229220231229162227", "finInstrmId": { "isin": "FR0000052292" }, "shrhldrsDsclsrRcrdDt": { "dt": { "dt": "2023-12-29" } } }, "pgntn": { "lastPgInd": true, "pgNb": "1" }, "rspndgIntrmy": { "ctctPrsn": { "emailAdr": "ipb.asset.servicing@bnpparibas.com", "nm": "IPB ASSET SERVICING" }, "id": { "anyBIC": "BNPAGB22PBG" }, "nmAndAdr": { "adr": { "adrTp": 0, "bldgNb": "10", "ctry": "GB", "ctrySubDvsn": "LONDON", "pstCd": "NW16AA", "strtNm": "HAREWOOD AVENUE", "twnNm": "LONDON" }, "nm": "BNP PARIBAS PRIME BROKERAGE" } } } }
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How about this
| makeresults
| eval Properties.appHdr = "{
\"fr\": {
\"fiId\": {
\"finInstnId\": {
\"bicfi\": \"BNPAGB22PBG\"
}
}
},
\"to\": {
\"fiId\": {
\"finInstnId\": {
\"bicfi\": \"SICVFRPPEII\"
}
}
},
\"bizMsgIdr\": \"res1caf3c2ac2b3b6d180ff0001aa7eefab\",
\"msgDefIdr\": \"seev.047.001.02\",
\"creDt\": \"2024-01-11T21:03:56.000Z\"
}"
| fields - _time
```Generate test event```
| spath input=Properties.appHdr
| table bizMsgIdr *- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Both these options are not working and splunk is not able to extract the bizMsgIdr from the field Properties.appHdr .
Can you please provide some other way to extract this text.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How about this
| makeresults
| eval Properties.appHdr = "{
\"fr\": {
\"fiId\": {
\"finInstnId\": {
\"bicfi\": \"BNPAGB22PBG\"
}
}
},
\"to\": {
\"fiId\": {
\"finInstnId\": {
\"bicfi\": \"SICVFRPPEII\"
}
}
},
\"bizMsgIdr\": \"res1caf3c2ac2b3b6d180ff0001aa7eefab\",
\"msgDefIdr\": \"seev.047.001.02\",
\"creDt\": \"2024-01-11T21:03:56.000Z\"
}"
| fields - _time
```Generate test event```
| spath input=Properties.appHdr
| table bizMsgIdr *- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's generally not the best idea to manipulate structured data with regexes if you can use the built-in functionality for handling the structure - like spath command or auto-kv functionality. Even if your data is guaranteed to be simple (you will never have an array or subobject as value), you don't have to worry of finding proper field boundaries, escaping and so on.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
why not this way?
| makeresults
| eval _raw = "{ \"shrhldrsIdDsclsrRspn\": { \"dsclsrRspnId\": \"0000537ede1c5e1084490000aa7eefab\", \"issrDsclsrReqRef\": { \"issrDsclsrReqId\": \"eiifr000005229220231229162227\", \"finInstrmId\": { \"isin\": \"FR0000052292\" }, \"shrhldrsDsclsrRcrdDt\": { \"dt\": { \"dt\": \"2023-12-29\" } } }, \"pgntn\": { \"lastPgInd\": true, \"pgNb\": \"1\" }, \"rspndgIntrmy\": { \"ctctPrsn\": { \"emailAdr\": \"ipb.asset.servicing@bnpparibas.com\", \"nm\": \"IPB ASSET SERVICING\" }, \"id\": { \"anyBIC\": \"BNPAGB22PBG\" }, \"nmAndAdr\": { \"adr\": { \"adrTp\": 0, \"bldgNb\": \"10\", \"ctry\": \"GB\", \"ctrySubDvsn\": \"LONDON\", \"pstCd\": \"NW16AA\", \"strtNm\": \"HAREWOOD AVENUE\", \"twnNm\": \"LONDON\" }, \"nm\": \"BNP PARIBAS PRIME BROKERAGE\" } } } }"
``` generate test data```
| spath
| table shrhldrsIdDsclsrRspn.issrDsclsrReqRef.issrDsclsrReqIdIf needed you can also use spath function with eval.
If you really want to use rex then this should work
| makeresults
| eval _raw = "{ \"shrhldrsIdDsclsrRspn\": { \"dsclsrRspnId\": \"0000537ede1c5e1084490000aa7eefab\", \"issrDsclsrReqRef\": { \"issrDsclsrReqId\": \"eiifr000005229220231229162227\", \"finInstrmId\": { \"isin\": \"FR0000052292\" }, \"shrhldrsDsclsrRcrdDt\": { \"dt\": { \"dt\": \"2023-12-29\" } } }, \"pgntn\": { \"lastPgInd\": true, \"pgNb\": \"1\" }, \"rspndgIntrmy\": { \"ctctPrsn\": { \"emailAdr\": \"ipb.asset.servicing@bnpparibas.com\", \"nm\": \"IPB ASSET SERVICING\" }, \"id\": { \"anyBIC\": \"BNPAGB22PBG\" }, \"nmAndAdr\": { \"adr\": { \"adrTp\": 0, \"bldgNb\": \"10\", \"ctry\": \"GB\", \"ctrySubDvsn\": \"LONDON\", \"pstCd\": \"NW16AA\", \"strtNm\": \"HAREWOOD AVENUE\", \"twnNm\": \"LONDON\" }, \"nm\": \"BNP PARIBAS PRIME BROKERAGE\" } } } }"
``` generate test data```
| rex "\"issrDsclsrReqId\"\s*:\s*\"(?<issrDsclsrReqId>[^\"]+)\""
| table issrDsclsrReqIdr. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is not working and no result in the column issrDsclsrReqId.
Is it possible to extract the value of "bizMsgIdr": from the field Properties.appHdr ?
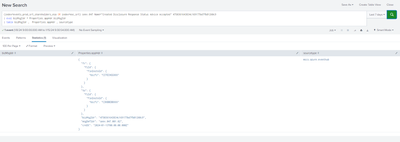
Splunk COmmand :
`macro_events_prod_srt_shareholders_esa` sourcetype ="mscs:azure:eventhub" Name="Received Disclosure Response Command" "res1caf3c2ac2b3b6d180ff0001aa7eefab".
Result in the column Properties.appHdr :
{
"fr": {
"fiId": {
"finInstnId": {
"bicfi": "BNPAGB22PBG"
}
}
},
"to": {
"fiId": {
"finInstnId": {
"bicfi": "SICVFRPPEII"
}
}
},
"bizMsgIdr": "res1caf3c2ac2b3b6d180ff0001aa7eefab",
"msgDefIdr": "seev.047.001.02",
"creDt": "2024-01-11T21:03:56.000Z"
}
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this is json, like you already has, it's easier and better to use spath to extract those.
Based on your screenshot you should have this already on field Properties.appHdr.bizMsgIdr . In that case you can try e.g
...
|rename Properties.appHdr.bizMsgIdr as bizMsgIdrif you really need to rename/use short version. Another option is use
...
| eval bizMsgIdr = Properties.appHdr.bizMsgIdr