Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Search shows zero results when searching a field d...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Search shows zero results when searching a field defined by search time extraction
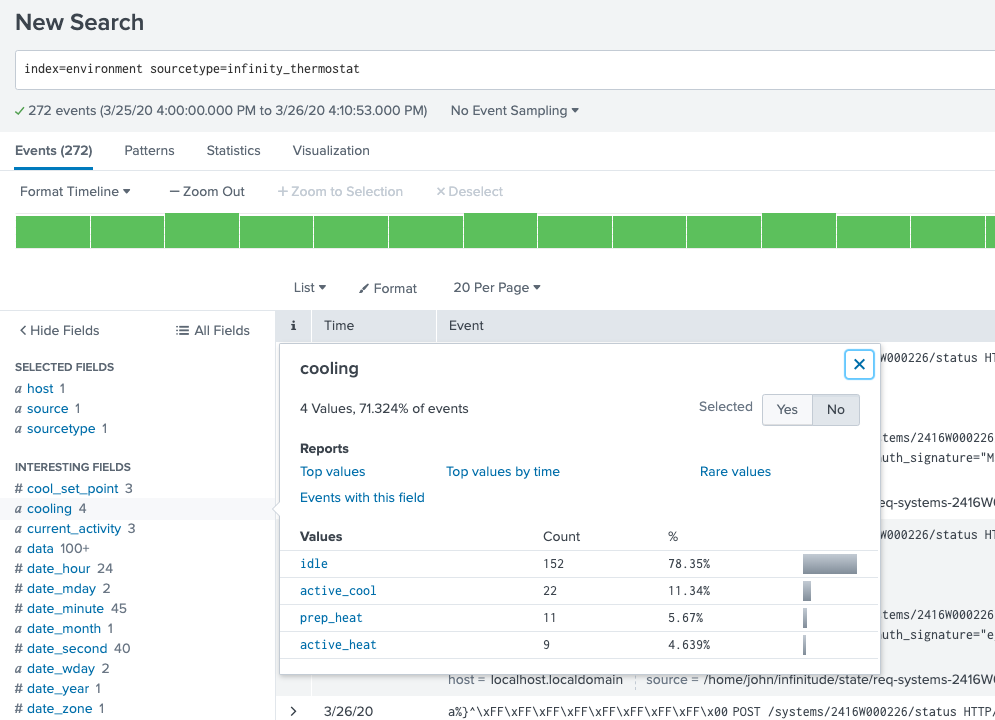
index=environment sourcetype=infinity_thermostat < shows all the extracted fields and values under "Interesting Fields">
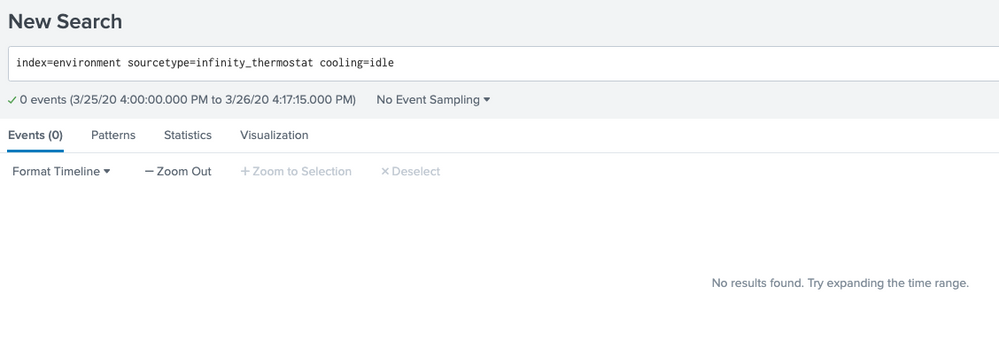
When I click and interesting field, see it's values and select a value (which adds it to the search), zero results are returned. Is this a bug in recent versions?
I've seen other "similar" posts and some talk about workarounds such as fields.conf, but this is pretty straight forward and the search time extractions are working, just not searchable when used in the search.
cooling=idle is the example I'm using which returns zero, cooling=idle* (zero results), cooling=idl* (zero results), cooling=id* (results), cooling=i* (results), cooling=* (all results), cooling=*idle (results)
Thank you for any thoughts/help
Screenshots attached showing the issue.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is a classic example of the field.conf problem so why are you doubting the appropriateness and efficacy? I will reiterate what you have already read:
If your values are not separated by major/minor-breakers (segmenters.conf), then they will not appear as indexed values in your tsidx so you have to tell the Search Head that these fields are not indexed fields by adding this to fields.conf:
[cooling]
INDEXED_VALUE = false
See details here:
https://www.splunk.com/blog/2011/10/07/cannot-search-based-on-an-extracted-field.html
BE CAREFUL! This is a GLOBAL setting and will effect all fields named cooling so you would be best off naming this field something that is uncommon (unlikely to be used by anybody else anywhere else).
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have a couple of questions:
1) Isn't it the case that this was fixed after version 4.3? That is what's noted in the document linked in the explanation. We're seeing this behavior, and we're on cloud 8.0.x.
2) It's a global change to affect field.conf - is that the same for affecting segmenters.conf?