Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Parse Email Subject and populate fields
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Splunkers!
Im running a very simple query to get the subject of all the emails we are getting. Something like this:
index=o365_email_data
|table Subject
Results look like this:
| Subject |
| Ticket ID: INC3333333 - Prio: 1 - High- "Description of the Incident" - has been updated |
| Ticket ID: INC1111111 - Prio: 4 - Low- "Description of the Incident" - has been resolved |
| Ticket ID: INC2222222 - Prio: 3 - Normal - "Description of the Incident" - has been created |
What I would like to accomplish is to be able to parse certain parts of that Subject and fill a table like this:
| Ticket | Priority | Description | Status |
| INC3333333 | High | Description of the Incident | updated |
| INC1111111 | Low | Description of the Incident | resolved |
| INC2222222 | Normal | Description of the Incident | created |
This resembles a lot like the "Text to Column" function in Excel. Im completely lost on how I can achieve this.
Many thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The rex command is your friend to do this in search:
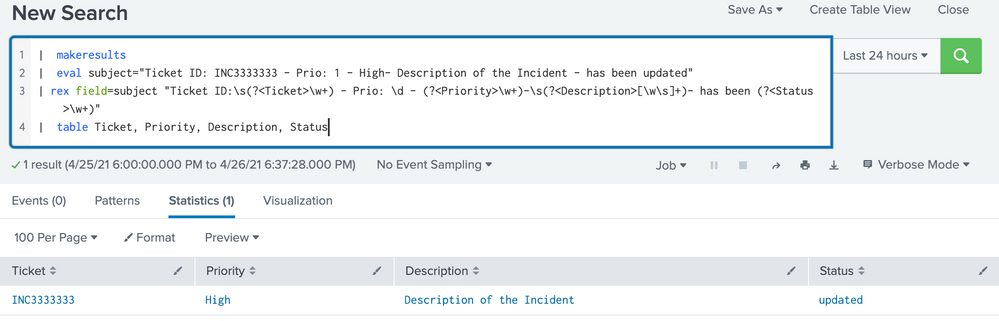
Here is the run anywhere search for the sample event above:
| makeresults
| eval subject="Ticket ID: INC3333333 - Prio: 1 - High- Description of the Incident - has been updated"
| rex field=subject "Ticket ID:\s(?<Ticket>\w+) - Prio: \d - (?<Priority>\w+)-\s(?<Description>[\w\s]+)- has been (?<Status>\w+)"
| table Ticket, Priority, Description, Status
You can also add these field extractions to your sourcetype, so the fields get parsed out automatically whenever you search.
HTH, Happy Splunking!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The rex command is your friend to do this in search:
Here is the run anywhere search for the sample event above:
| makeresults
| eval subject="Ticket ID: INC3333333 - Prio: 1 - High- Description of the Incident - has been updated"
| rex field=subject "Ticket ID:\s(?<Ticket>\w+) - Prio: \d - (?<Priority>\w+)-\s(?<Description>[\w\s]+)- has been (?<Status>\w+)"
| table Ticket, Priority, Description, Status
You can also add these field extractions to your sourcetype, so the fields get parsed out automatically whenever you search.
HTH, Happy Splunking!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just had an AHA moment, thanks so much for showing me how to do this 🙂