Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Multivalue field extraction
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, I'm struggling to get this extracted correctly so it's usable.
The raw data is presented as:
Privileges: SeSecurityPrivilege
SeBackupPrivilege
SeRestorePrivilege
SeTakeOwnershipPrivilege
SeDebugPrivilege
SeSystemEnvironmentPrivilege
SeLoadDriverPrivilege
SeImpersonatePrivilege
SeAssignPrimaryTokenPrivilege
By default, only the first entry is assigned to the field eg:
"SeSecurityPrivilege"
I can extract the remaining lines into the field using the regex "Privileges:\t(?P(\w+\s+|\t\t\t\w+\s+)+)", which returns this:
"SeSecurityPrivilege SeBackupPrivilege SeRestorePrivilege SeTakeOwnershipPrivilege SeDebugPrivilege SeSystemEnvironmentPrivilege SeLoadDriverPrivilege SeImpersonatePrivilege"
Now what I need is to split each of these into the Privileges field as separate values.
These values are not a static number of entries, so Privileges could contain anything between 1 and 10 lines.
Any advice would be great as the docs and answers I've read don't seem to help this situation.
TIA
Steve
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Give this a try
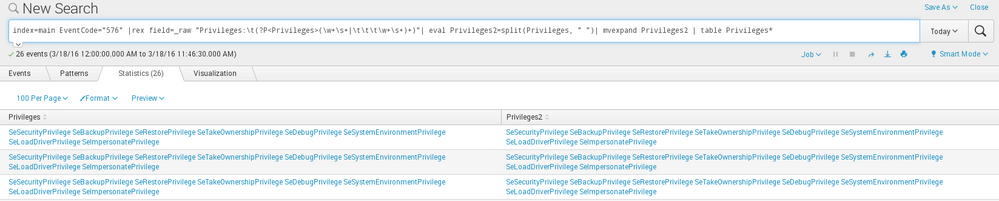
index=main EventCode="576" |rex field=_raw "Privileges:\t(?P<Privileges>(\w+\s+|\t\t\t\w+\s+)+)" | rex field=Privileges max_match=0 "(?<Privilege>\S+)\s+" | mvexpand Privilege
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks to everyone that has offered help. Much appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi cdstealer
Try to add this, after your field extraction.
main search | rex field=_raw ... | makemv delim=" " Privileges | mvexpand Privileges
Hope it helps.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Give this a try
index=main EventCode="576" |rex field=_raw "Privileges:\t(?P<Privileges>(\w+\s+|\t\t\t\w+\s+)+)" | rex field=Privileges max_match=0 "(?<Privilege>\S+)\s+" | mvexpand Privilege
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Perfect! I think you've solved a couple of my past questions. So thank you very much again 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi again, Now I'm struggling transferring the search into props/transforms. I'm probably missing something simple.
props.conf:
EXTRACT-Privileges = Privileges:\t(?P<Privileges>(\w+\s+|\t\t\t\w+\s+)+)
REPORT-fields = privilege
transforms.conf:
[privilege]
SOURCE_KEY = Privileges
REGEX = "(?<privilege>\S+)\s+)
REPEAT_MATCH = true
MV_ADD = true
So the new field that contains the extracted values is not happening.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello, did you manage to solve this ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You have an extra " in front of your REGEX in transforms.conf.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
try :
your_base_search|rex field=_raw "Privileges:\t(?P<Privileges>(\w+\s+|\t\t\t\w+\s+)+)"| eval Privileges=split(field_name_extraction, " ")| mvexpand Privileges|...
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi fdi01, Thanks. Unfortunately this does not change the output.
Steve
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
your rex |rex field=_raw "Privileges:\t(?P<Privileges>(\w+\s+|\t\t\t\w+\s+)+)"| capture all results in Privileges field ???
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content