Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Join the Conversation
Without signing in, you're just watching from the sidelines. Sign in or Register to connect, share, and be part of the Splunk Community.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Multiple values - mvexpand not doing what I expect
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dbcase
Motivator
02-19-2018
11:44 AM
Hi ,
I have a query that looks like this
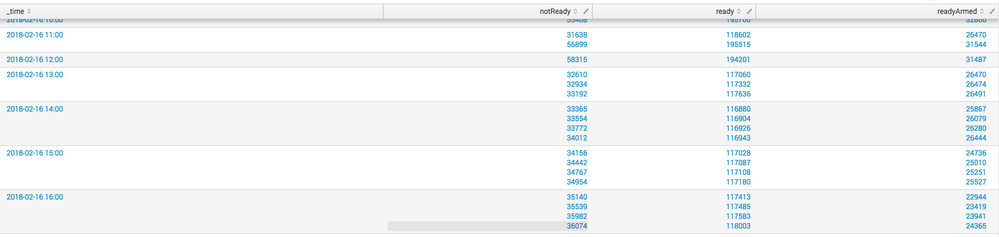
earliest=-100hr index=blahalarm STATUS=readyArmed OR STATUS=ready OR STATUS=notReady|mvexpand notReady|mvexpand ready|mvexpand readyArmed|mvexpand _time|timechart span=1hr values(field2) by STATUS
but the resulting dataset comes back as this. I'm confused, why wouldn't mvexpand create multiple events?
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dbcase
Motivator
02-19-2018
11:55 AM
FIxed it. My data was coming in with 15min increments but my span=1hr, once I set my span to 15min all is well
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
dbcase
Motivator
02-19-2018
11:55 AM
FIxed it. My data was coming in with 15min increments but my span=1hr, once I set my span to 15min all is well
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
elliotproebstel
Champion
02-19-2018
11:54 AM
Doesn't the final timechart span=1h bring the events back into 1h buckets? The result looks like what I'd expect. Can you say more about what you're trying to achieve?
Got questions? Get answers!
Join the Splunk Community Slack to learn, troubleshoot, and make connections with fellow Splunk practitioners in real time!
Meet up IRL or virtually!
Join Splunk User Groups to connect and learn in-person by region or remotely by topic or industry.
Get Updates on the Splunk Community!
Announcing Modern Navigation: A New Era of Splunk User Experience
We are excited to introduce the Modern Navigation feature in the Splunk Platform, available to both cloud and ...
Modernize your Splunk Apps – Introducing Python 3.13 in Splunk
We are excited to announce that the upcoming releases of Splunk Enterprise 10.2.x and Splunk Cloud Platform ...
Step into “Hunt the Insider: An Splunk ES Premier Mystery” to catch a cybercriminal ...
After a whole week of being on call, you fell asleep on your keyboard, and you hit a sequence of buttons that ...