Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Lookup matching field and bring in new field from ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lookup matching field and bring in new field from lookup
Hello, I've been banging my head against the wall over the last like two hours over this and figured I should just post since I don't find Splunk documentation that helpful, detailed, or plentiful.
Objective: What I want to do is we have the results from a nice search query. Now we want to take the full hostname and compare that to a field in the Lookup and from there bringing in an related alternate field from that lookup.
The example hopefully is easy to understand and something quick I'm just screwing up.
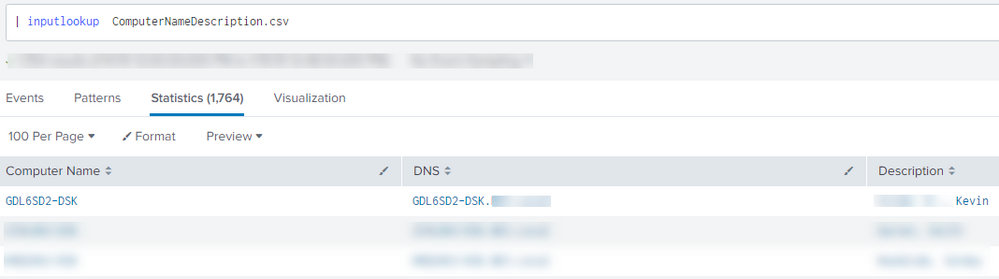
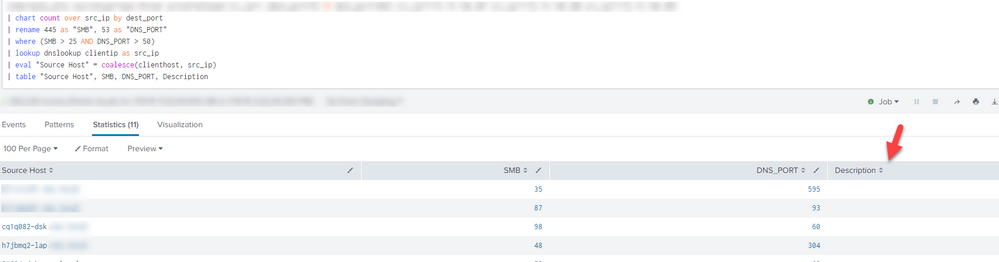
So our query below is returning us the following:
What I want to accomplish is use the CSV lookup file I have, use the clienthost field and compare that against the DNS field in my lookup file. And from there automatically pull in the matching related value from Description. Does that make sense hopefully. I tried every variation of using | | lookup ComputerNameDescription.csv DNS as clienthost OUTPUT Description, etc. Idk. I tried like 20 different ways and it's not looking it up, matching and letting me bring in the matching Description.
Can someone please tell me what we're doing wrong.
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No real answer yet, all suggestions have failed so far.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@kamlesh_vaghela
I have tried that as one of the variations when I was going through the documentation, but it still doesn't work. See my image below:
@jkat54
Yes there is a match. I'm matching the DNS field in the CSV to my clienthost field in my events which should align. See images.
Any further ideas?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Not in your search sample you gave.
You need to give lookup command more details.
See the lookup command documentation Kamlesh provided.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try swapping clienthost and DNS around
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don’t see the ip fields in your lookup.
So there’s nothing to match/join it to.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@rpatelnes
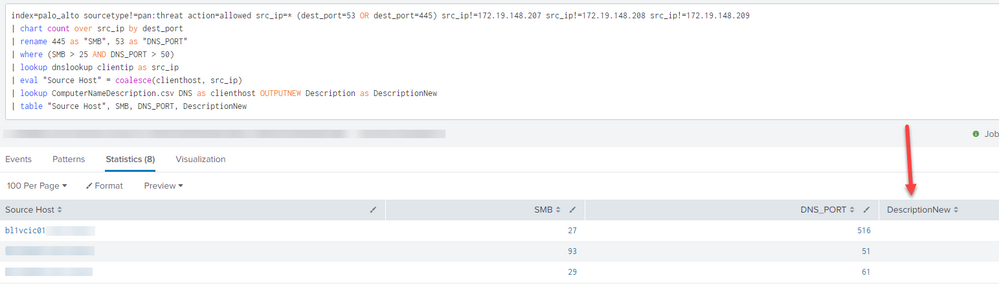
Have you tried OUTPUTNEW option of lookup command ?
Can you please confirm DescriptionNew returning anything using below lookup command?
| lookup ComputerNameDescription.csv DNS as clienthost OUTPUTNEW Description as DescriptionNew
Ref:
https://docs.splunk.com/Documentation/SplunkCloud/7.1.3/SearchReference/Lookup