Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Junk characters showing when I use stats with list...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Junk characters showing when I use stats with list command to get the logins and logout of a VPN
Dear Community Members ,
In splunk cloud instance :
I am trying to get VPN login and logout for users in a single table sorted by Username and Time.
The query is as below:
eventtype="my_eventtype_1" eventtype="my_eventtype_2" (((EventIDValue=gateway-auth OR EventIDValue=clientlessvpn-login) EventStatus=success SourceUserName!="pre-logon") OR Stage=logout) | stats list(EventIDValue) as Activity,list(_time) as Time by SourceUserName |rename SourceUserName as username|convert ctime(Time)|eval username=upper(username)|sort username,-Time
The search is for a period of 24 hours.
I am getting the data but along with it, I see junk characters (if I may call them so).
Kindly help to understand how to resolve the same.
I also tried adding limit=0 along with stats command but no use.
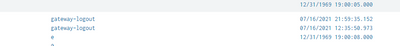
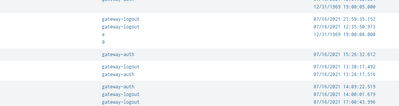
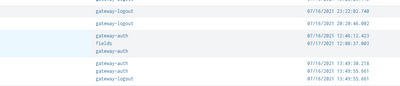
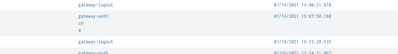
Below is the screenshot of the fields. I have not shown the username field for security reasons.
I have used a similar query for another VPN and it works fine there and I don't see these characters !
Regards,
Abhishek Singh
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
eventtype="my_eventtype_1" eventtype="my_eventtype_2" (((EventIDValue=gateway-auth OR EventIDValue=clientlessvpn-login) EventStatus=success SourceUserName!="pre-logon") OR Stage=logout) | stats list(EventIDValue) as Activity,list(_time) as Time by SourceUserName |convert ctime(Time)|sort SourceUserName,-Time
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
More examples of the issue.