Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Iterate search over multiple field values
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Iterate search over multiple field values
Hi,
I've created a search which is based on 1 field value but I need the search to run over many field values. Rather than many repeating lines.
What is the best way to do this? I know what the field values are before the search too.
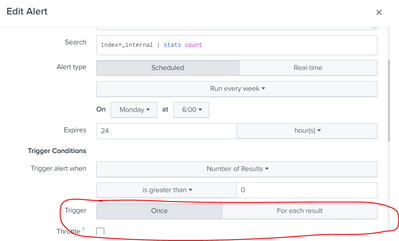
It will be an alert where if 1 or more field values match the end criteria, an email is sent. I only want 1 email, not 1 for every field value.
Thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
you can use filed= value1 OR filed=value2 and so on in the search. You can always configure the alert to send an email for each result OR group of results.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To give some more detail of my search, it takes the field value and look at the past hour of data, compares that to the past week of data to get the percent difference. Then show result where diff > x.
This needs to done for each field value though and I don't know how to do that without a lot of evals, addtotals, etc. I want to be able to do a nice clean short search regardless of the field value, and pass in the field value.
Thanks.