Join the Conversation
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Issue with regex
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is the event :
02OCT2017_16:46:47.212 130880:140149567481600 INFO event.py:177 root event = {"hopTrace": {"hops": [{"machine": {"nodeId": 569}, "application": {"processId": 19295, "processName": "udrqssvc.tsk", "appName": "DRQS"}, "authenticatedUser": {"uuid": 10095155}}]}, "event": {"eventType": "DRQS UPDATED", "drqsNumber": 107516809(FIELD5), "newHeader": {"status": "Q", "function": "N539", "billToId": 5028, "yellowKey": "", "billToType": "HIER", "lastUpdateTime": "2017-10-02T20:46:47.000+00:00", "type": "IW", "creatorUuid": 1603009, "slaCategory": -1, "summary": "MM/DD n539 hardware failure IBM PMR: 24465.L6Q.000", "queue": "", "timeClosed": "1899-12-31T05:00:00.000+00:00", "ouTypeCode": 0, "routeToGroup": 270(FIELD4), "ouTypeDescription": "", "tsCustomerNumber": 0, "closedUuid": 0, "lastUpdateUuid": 10095155, "createTime": "2017-09-29T12:00:48.000+00:00", "ownerUuid": 2984495}, "logNotes": [{"logNoteId": "1049598095", "timestamp": "2017-10-02T20:46:47.141+00:00", "authorUuid": 10095155, "logText": [{"text": "Note added from offline, remote machine 208\n", "textType": "DEEMPHASIZED"}, {"text": "{FIFW PRQS 160269881(FIELD6)} submitted to take N539(FIELD1) (N539) offline on Tue Oct 03 2017 19:00:00 GMT-0400 (EDT)(FIELD2) for HARDWARE REPAIRS(FIELD3)\n", "textType": "NORMAL"}], "isAutomated": true}]}, "metadata": {"publishId": "121785005", "publishTime": "2017-10-02T16:46:47.189-04:00"}}
From the above event I want to create a statistics table with Field1-Fileds 6
I have highlighted the needed fields as bold . I get some of them but not all 6 fields
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Please check this rex query... (if the event got different words, then rex needs to be adjusted)
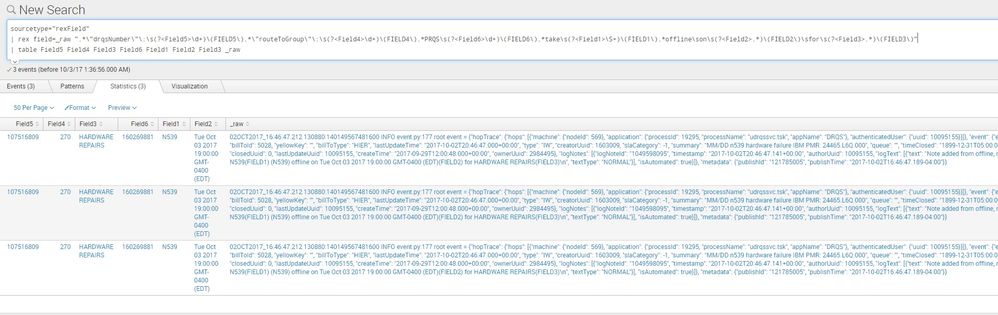
Updated - the base query
contextName=olliebot service_name=olliebot source="/bb/logs/vcon/olliebot.log.2017*" AND (PRQS AND submitted)
| rex field=_raw ".*\"drqsNumber\"\:\s(?<Field5>\d+)\(FIELD5\).*\"routeToGroup\"\:\s(?<Field4>\d+)\(FIELD4\).*PRQS\s(?<Field6>\d+)\(FIELD6\).*take\s(?<Field1>\S+)\(FIELD1\).*offline\son\s(?<Field2>.*)\(FIELD2\)\sfor\s(?<Field3>.*)\(FIELD3\)"
| table Field5 Field4 Field3 Field6 Field1 Field2 Field3 _raw
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry forgot to mention that I tried that but the problem is the field is
Tue Oct 03 2017 19:00:00 GMT-0400 (EDT)(FIELD2
and sorting by field2 it goes alphabetically and not the actual dates
Can the day be eliminated somehow ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can the day be eliminated somehow - meaning, you want to sort by the date(03 on the date - Tue Oct 03 2017 19:00:00 GMT-0400) ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Basically it sorts as Oct 03 2017 19:00:00 GMT-0400)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It shouldn't sort by the days
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
not getting your question..
maybe, please check this post for sorting a date value -
https://answers.splunk.com/answers/290983/days-in-alphabetical-order-but-need-to-be-in-day-o.html
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I mean when am sorting the results by date this is the table I get :
Fri Oct 06 2017 13:00:00 GMT-0400 (EDT)
Sat Oct 07 2017 12:00:00 GMT-0400 (EDT)
Thu Oct 05 2017 06:00:00 GMT-0400 (EDT)
Tue Oct 03 2017 13:00:00 GMT-0400 (EDT)
Tue Oct 03 2017 18:00:00 GMT-0400 (EDT)
Tue Oct 03 2017 18:00:00 GMT-0400 (EDT)
Tue Oct 03 2017 19:00:00 GMT-0400 (EDT)
Wed Oct 04 2017 13:00:00 GMT-0400 (EDT)
Wed Oct 04 2017 13:00:00 GMT-0400 (EDT)
Wed Oct 04 2017 19:30:00 GMT-0400 (EDT)
and its based on the alphabetical order and not the actual dates
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
generally there is an extracted field "date_mday", which is the day-month. you can try to sort using this one...
| table HOSTNAME , DRQS , PRQS , WINDOW , MAINTENANCE Field2 | fillnull value="NULL" | search HOSTNAME!="NULL" AND DRQS!="NULL" AND PRQS!="NULL" AND WINDOW!="NULL" | dedup HOSTNAME | sort date_mday
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @bharpur183, Can you please accept this as answer, so that it will be marked as solved, while you do that you will get karma points as well.. you can upvote the answer and comments too 😉
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
| rex field=_raw "(?<field6>\S+) submitted to take (?<field1>\S+) .* offline on (?<field2>.*) for (?<field3>[^\"]+)\""
| rex field=_raw "\"drqsNumber\": (?<field5>\S+),"
| rex field=_raw "\"routeToGroup\": (?<field4>\S+),"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
get an error :
Error in 'rex' command: Encountered the following error while compiling the regex '(?.*) for (?[^"]+)"': Regex: syntax error in subpattern name (missing terminator)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've updated the query
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks . That works . can you please provide the same for fields 1 and field 5 ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Updated. Please look at the rex command to learn how this command works.
http://docs.splunk.com/Documentation/Splunk/latest/SearchReference/Rex
http://docs.splunk.com/Documentation/Splunk/latest/Search/SPLandregularexpressions