Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Ignore events within a timespan?
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ignore events within a timespan?
bmorgenthaler
Path Finder
11-03-2020
06:53 PM
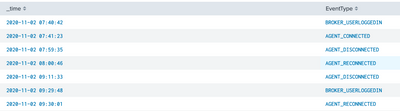
Is it possible to drop events if they occur within a certain timespan of each other? I'm specifically looking at VMware View logs and trying to corelate external user login sessions. Normally there is a BROKER_USERLOGGEDIN event and then AGENT RECONNECT/CONNECT events. Unfortunately everyonce in a while there is a network hiccup and a client disconnects/reconnects without a BROKER_USERLOGGEDIN event (like the attached picture).
I want to ignore/drop any EventType=AGENT_DISCONNECT and EventType=AGENT_RECONNECT if they happen within 60 seconds.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MuS
Legend
11-03-2020
07:16 PM
Hi bmorgenthaler ,
you can use `streamstats` to calculate the time difference and filter on that like this:
your base search here
| streamstats current=f last(_time) AS l_time last(EventType) AS l_EventType by EventType
| eval diff = _time - l_time
| where diff < 60 AND l_EventType=="AGENT_DISCONNECT" AND EventType=="AGENT_RECONNECT" This might needs tuning but will give you a starting point.
Hope this helps ...
cheers, MuS
Career Survey
First 500 qualified respondents will receive a $20 gift card! Tell us about your professional Splunk journey.
Get Updates on the Splunk Community!
Community Content Calendar, September edition
Welcome to another insightful post from our Community Content Calendar! We're thrilled to continue bringing ...
Splunkbase Unveils New App Listing Management Public Preview
Splunkbase Unveils New App Listing Management Public PreviewWe're thrilled to announce the public preview of ...
Leveraging Automated Threat Analysis Across the Splunk Ecosystem
Are you leveraging automation to its fullest potential in your threat detection strategy?Our upcoming Security ...